What is SSH in the IoT Network: Secure Shell Explained
Secure Shell (SSH) plays a crucial role in securing IoT networks, ensuring data integrity, and protecting devices from unauthorized access. As the Internet of Things (IoT) continues to expand, the importance of robust security protocols becomes paramount. SSH offers a reliable solution for encrypted communication between devices, safeguarding sensitive information from cyber threats.
In today's interconnected world, IoT devices are rapidly increasing in number, creating new opportunities while also introducing significant security challenges. Without proper security measures, these devices can become entry points for cyberattacks, leading to data breaches and privacy violations. This is where SSH comes into play, providing a secure channel for remote access and data transmission.
This article will explore the fundamentals of SSH in IoT networks, its applications, benefits, and best practices for implementation. Whether you're a network administrator, developer, or simply someone interested in IoT security, this guide will provide you with the knowledge you need to understand and implement SSH effectively.
Introduction to SSH
Secure Shell (SSH) is a cryptographic network protocol designed to provide secure communication over unsecured networks. Initially developed in 1995 by Tatu Ylönen, SSH has become a standard tool for securing remote access and data transfer. It encrypts all data exchanged between devices, ensuring confidentiality, integrity, and authentication.
Why SSH is Essential
SSH is essential for protecting sensitive information from unauthorized access and eavesdropping. In the context of IoT, where devices often communicate over public networks, SSH ensures that data remains secure even when transmitted across insecure channels. Its ability to authenticate users and devices adds an additional layer of security, preventing unauthorized access.
SSH in IoT Networks
IoT networks consist of numerous interconnected devices, each requiring secure communication to function effectively. SSH plays a vital role in securing these networks by providing a secure channel for remote access, configuration, and data transfer. Its robust encryption and authentication mechanisms make it an ideal choice for protecting IoT devices.
Applications of SSH in IoT
- Secure remote access to IoT devices
- Encrypted data transfer between devices
- Automated configuration and management
- Secure firmware updates
Benefits of Using SSH
Implementing SSH in IoT networks offers several benefits, including enhanced security, ease of use, and scalability. Below are some of the key advantages of using SSH:
Improved Security
SSH encrypts all data transmitted between devices, making it difficult for attackers to intercept or tamper with sensitive information. Its strong authentication mechanisms ensure that only authorized users and devices can access the network.
Scalability
SSH is highly scalable and can be used to secure communications in large IoT networks with thousands of devices. Its ability to handle multiple connections simultaneously makes it suitable for enterprise-level deployments.
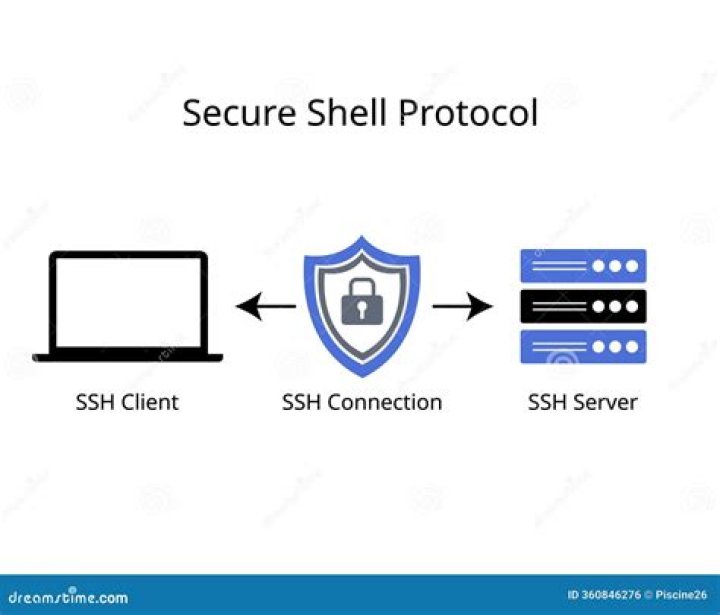
How SSH Works
SSH operates by establishing a secure connection between two devices using a combination of symmetric and asymmetric encryption. The process begins with a handshake, during which the devices exchange encryption keys and authenticate each other. Once the connection is established, all data transmitted between the devices is encrypted, ensuring its confidentiality and integrity.
Key Components of SSH
- Encryption: SSH uses advanced encryption algorithms to protect data in transit.
- Authentication: SSH supports various authentication methods, including password-based and public key authentication.
- Integrity: SSH ensures data integrity by using cryptographic hashes to detect any tampering during transmission.
Security Features of SSH
SSH offers several security features that make it an ideal choice for securing IoT networks. These features include:
Public Key Authentication
Public key authentication allows devices to authenticate each other without the need for passwords, reducing the risk of brute-force attacks. Each device generates a pair of public and private keys, which are used to verify its identity.
Encryption Algorithms
SSH supports a wide range of encryption algorithms, including AES, Blowfish, and 3DES. These algorithms ensure that data remains secure even when transmitted over unsecured networks.
Common SSH Attacks
Despite its robust security features, SSH is not immune to attacks. Some common SSH attacks include:
Brute-Force Attacks
Brute-force attacks involve repeatedly guessing passwords until the correct one is found. To mitigate this threat, it is recommended to use public key authentication and disable password-based login.
Man-in-the-Middle Attacks
Man-in-the-middle attacks occur when an attacker intercepts and alters communications between two devices. SSH protects against these attacks by using digital certificates to verify the identity of devices.
Best Practices for SSH in IoT
To ensure the security of your IoT network, it is essential to follow best practices for SSH implementation. Below are some recommendations:
Use Strong Passwords
If password-based authentication is used, ensure that passwords are strong and complex. Avoid using default passwords and change them regularly.
Enable Public Key Authentication
Public key authentication provides a more secure alternative to password-based login. By enabling this feature, you can reduce the risk of brute-force attacks.
Tools for SSH Implementation
Several tools and libraries are available for implementing SSH in IoT networks. Some popular options include:
OpenSSH
OpenSSH is a widely used implementation of the SSH protocol, providing robust security features and ease of use. It is available for a variety of platforms, including Linux, macOS, and Windows.
Dropbear
Dropbear is a lightweight SSH server designed for use in embedded systems. Its small footprint and low resource requirements make it ideal for IoT devices with limited processing power.
Case Studies of SSH in IoT
Several organizations have successfully implemented SSH in their IoT networks, achieving significant improvements in security and efficiency. Below are two case studies:
Case Study 1: Smart City Infrastructure
A smart city in Europe implemented SSH to secure communications between its IoT devices, including traffic lights, surveillance cameras, and environmental sensors. The use of SSH ensured that sensitive data, such as video feeds and air quality readings, remained secure and protected from unauthorized access.
Case Study 2: Industrial IoT
An industrial manufacturer used SSH to secure remote access to its IoT devices, enabling engineers to monitor and manage equipment from anywhere in the world. This implementation resulted in improved operational efficiency and reduced downtime.
The Future of SSH in IoT
As IoT continues to evolve, the role of SSH in securing these networks will become increasingly important. Advances in encryption algorithms and authentication methods will further enhance the security of SSH, making it an even more effective tool for protecting IoT devices.
Emerging Trends
Some emerging trends in SSH include the use of quantum-resistant encryption algorithms and biometric authentication. These advancements will help ensure the long-term security of IoT networks as new threats emerge.
Kesimpulan
In conclusion, SSH is a vital tool for securing IoT networks, providing robust encryption and authentication mechanisms to protect sensitive data and devices. By following best practices and staying informed about emerging trends, organizations can ensure the security of their IoT networks and protect against cyber threats.
We invite you to share your thoughts and experiences with SSH in IoT networks in the comments section below. Additionally, feel free to explore other articles on our site for more insights into IoT security and related topics.