VNC SSH IoT Free Download: A Comprehensive Guide to Secure Remote Access
Accessing devices remotely has become an essential part of modern technology, and VNC SSH IoT free download plays a crucial role in enabling secure remote connections. Whether you're a developer, IT professional, or hobbyist, understanding how to leverage VNC over SSH for IoT devices can significantly enhance your productivity and security. This guide will walk you through everything you need to know about VNC SSH IoT free download, from setup to advanced configurations.
In today's interconnected world, IoT devices are everywhere, from smart homes to industrial automation. However, managing these devices remotely requires robust solutions that prioritize security and ease of use. VNC SSH IoT free download offers a powerful combination of tools that allow you to connect and control your devices securely from anywhere.
By the end of this article, you'll have a thorough understanding of what VNC SSH IoT free download entails, its benefits, and how to implement it effectively. Let's dive in and explore this fascinating technology that is transforming the way we interact with IoT devices.
Introduction to VNC SSH IoT Free Download
VNC SSH IoT free download is a solution that enables secure remote access to IoT devices. It combines the power of Virtual Network Computing (VNC) with the security of Secure Shell (SSH). This combination allows users to remotely control and manage IoT devices while ensuring that their connection remains protected from unauthorized access.
As the Internet of Things continues to grow, the need for secure remote management solutions becomes increasingly important. VNC SSH IoT free download addresses this need by providing a cost-effective and reliable way to manage IoT devices from anywhere in the world.
In this section, we'll explore the basics of VNC SSH IoT free download, its applications, and why it's becoming a popular choice for IoT enthusiasts and professionals alike.
What is VNC and How Does It Work?
VNC, or Virtual Network Computing, is a graphical desktop sharing system that allows you to remotely control another computer. It transmits keyboard and mouse events from one computer to another and returns the screen updates over the network. VNC is platform-independent, meaning it can be used across different operating systems.
Key Features of VNC
- Platform independence
- Remote control capabilities
- Screen sharing
- File transfer
VNC operates on a client-server model, where the server is the machine being controlled, and the client is the machine initiating the connection. This makes it an ideal solution for managing IoT devices remotely, especially when combined with SSH for added security.
Understanding SSH and Its Importance
SSH, or Secure Shell, is a cryptographic network protocol that provides secure communication over unsecured networks. It is widely used for remote command-line login and other secure network services. SSH encrypts all data transmitted between the client and server, ensuring that sensitive information remains protected from eavesdropping and tampering.
When it comes to IoT devices, SSH plays a critical role in securing remote connections. By encrypting the communication between the VNC client and server, SSH ensures that unauthorized users cannot intercept or manipulate the data being transmitted.
Why Use SSH with VNC?
- Encryption of data
- Authentication of users
- Protection against man-in-the-middle attacks
Using SSH with VNC significantly enhances the security of your remote connections, making it an essential component of any IoT remote management solution.
Combining VNC and SSH for Enhanced Security
Combining VNC and SSH creates a powerful solution for securely managing IoT devices. By tunneling VNC traffic through an SSH connection, you can ensure that your remote access sessions remain encrypted and protected from potential threats.
This combination offers several advantages, including:
- End-to-end encryption
- Secure authentication
- Protection against unauthorized access
In addition to enhancing security, using VNC over SSH can also improve the performance of your remote connections by reducing latency and improving reliability.
Integrating VNC SSH with IoT Devices
Integrating VNC SSH with IoT devices requires careful planning and configuration. The first step is to ensure that your IoT devices support VNC and SSH protocols. Many modern IoT devices come with built-in support for these protocols, making integration straightforward.
Steps to Integrate VNC SSH with IoT Devices
- Install VNC server software on the IoT device
- Configure SSH on the IoT device
- Set up port forwarding if necessary
- Connect to the IoT device using a VNC client over SSH
By following these steps, you can successfully integrate VNC SSH with your IoT devices and enjoy the benefits of secure remote access.
Free Download Options for VNC SSH IoT
There are several free download options available for VNC SSH IoT solutions. These options cater to a wide range of users, from beginners to advanced users, and offer varying levels of functionality and support.
Popular VNC SSH IoT Free Download Options
- TightVNC
- RealVNC
- UltraVNC
- OpenSSH
When choosing a free download option, consider factors such as ease of use, compatibility with your IoT devices, and the level of support provided by the software vendor.
Step-by-Step Setup Guide
Setting up VNC SSH IoT involves several steps, including installing the necessary software, configuring the server and client, and establishing a secure connection. Below is a step-by-step guide to help you get started:
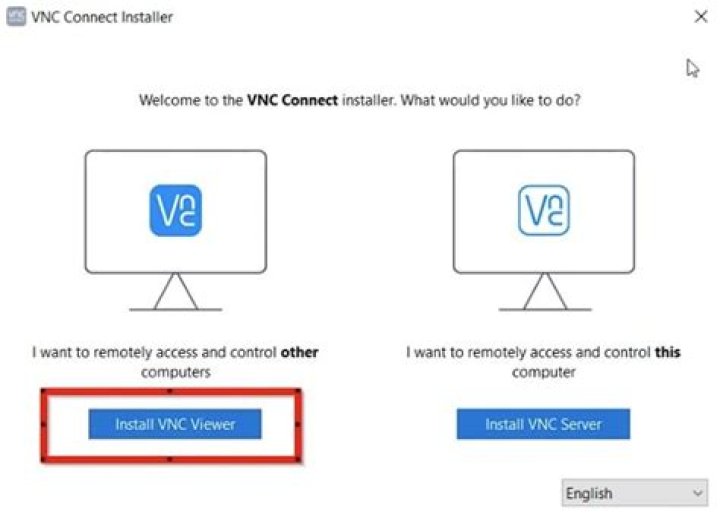
Step 1: Install VNC Server
Download and install a VNC server on your IoT device. Popular choices include TightVNC, RealVNC, and UltraVNC.
Step 2: Configure SSH
Set up SSH on your IoT device by installing an SSH server, such as OpenSSH. Configure the SSH server to listen on the default port (22) or a custom port if required.
Step 3: Connect Using VNC Client
Use a VNC client to connect to your IoT device over SSH. This can be done by configuring the VNC client to use an SSH tunnel or by using an SSH client to forward the VNC port.
By following these steps, you can successfully set up VNC SSH IoT on your devices and enjoy secure remote access.
Benefits of Using VNC SSH IoT
Using VNC SSH IoT offers numerous benefits, including:
- Enhanced security through encryption
- Improved remote management capabilities
- Cost-effective solution for IoT device management
- Platform independence
These benefits make VNC SSH IoT an attractive option for anyone looking to manage IoT devices remotely while maintaining a high level of security.
Security Tips for VNC SSH IoT
While VNC SSH IoT provides a secure way to manage IoT devices remotely, it's essential to follow best practices to ensure maximum security. Below are some security tips to keep in mind:
- Use strong passwords for VNC and SSH authentication
- Enable two-factor authentication whenever possible
- Regularly update your VNC and SSH software
- Monitor access logs for suspicious activity
By implementing these security tips, you can further enhance the security of your VNC SSH IoT setup and protect your devices from potential threats.
Troubleshooting Common Issues
Like any technology, VNC SSH IoT can encounter issues that may affect its performance. Below are some common issues and their solutions:
- Connection problems: Ensure that the VNC server and SSH server are properly configured and running.
- Slow performance: Optimize your network settings and reduce the screen resolution for faster connections.
- Authentication failures: Verify that your credentials are correct and that two-factor authentication is properly configured.
By addressing these common issues, you can ensure that your VNC SSH IoT setup runs smoothly and efficiently.
Conclusion
VNC SSH IoT free download provides a powerful and secure solution for managing IoT devices remotely. By combining the capabilities of VNC and SSH, you can enjoy enhanced security, improved performance, and greater flexibility in managing your devices.
We encourage you to explore the various free download options available and experiment with different configurations to find the setup that best suits your needs. Don't forget to follow best practices for security and regularly update your software to ensure maximum protection.
If you found this article helpful, please consider sharing it with others who may benefit from it. Feel free to leave a comment below with any questions or feedback you may have. Thank you for reading, and happy IoT management!


