SSH Into IoT Device Example: A Comprehensive Guide
SSH (Secure Shell) is an essential tool for securely accessing and managing IoT devices remotely. As IoT technology continues to expand, understanding how to use SSH effectively is critical for developers, network administrators, and tech enthusiasts alike. This article will provide a detailed explanation of SSH into IoT device examples, helping you master the process.
Whether you're configuring a smart home device or managing a fleet of industrial sensors, secure access is paramount. In this guide, we will explore the importance of SSH, step-by-step examples, and best practices for connecting to IoT devices securely. By the end, you'll have the knowledge and confidence to manage your IoT devices efficiently.
SSH into IoT device example scenarios are designed to provide hands-on experience for users who want to enhance their skills in remote device management. This guide will cover everything from basic setup to advanced troubleshooting techniques, ensuring that you can handle any challenge that comes your way.
What is SSH?
SSH, or Secure Shell, is a cryptographic network protocol used for secure communication between devices over an unsecured network. It provides a secure channel for remote command execution and file transfers. SSH into IoT device example applications often involve managing devices such as routers, smart home systems, or industrial sensors remotely.
Key features of SSH include:
- Encryption for secure data transmission
- Authentication mechanisms to verify user identity
- Support for various cryptographic algorithms
SSH is widely adopted due to its robust security features, making it ideal for IoT device management. According to a study by Statista, the global IoT market is projected to reach $1.1 trillion by 2026, underscoring the importance of secure communication protocols like SSH.
Overview of IoT Devices
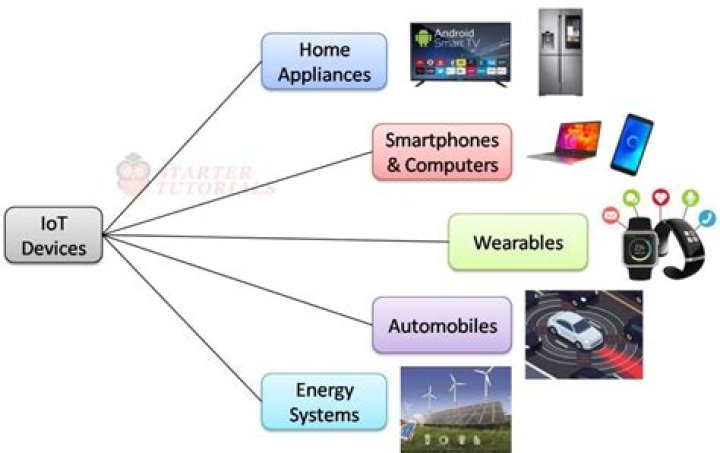
IoT (Internet of Things) refers to the network of physical devices embedded with sensors, software, and connectivity, enabling them to exchange data. Examples of IoT devices include smart thermostats, wearable health trackers, and industrial automation systems. SSH into IoT device example scenarios are crucial for managing these devices remotely.
Types of IoT Devices
IoT devices can be broadly categorized into three types:
- Consumer IoT: Smart home devices, wearables, and personal gadgets
- Enterprise IoT: Industrial sensors, asset tracking systems, and supply chain management tools
- Infrastructure IoT: Smart city solutions, utility grid monitoring, and transportation systems
Each type of IoT device requires specific configurations for SSH access. Understanding the unique requirements of your device is key to successful remote management.
Benefits of Using SSH for IoT Devices
Using SSH for IoT devices offers several advantages:
- Enhanced security through encryption
- Reliable remote access for device management
- Automation capabilities for repetitive tasks
- Compatibility with a wide range of devices
According to a report by Cisco, over 50 billion IoT devices are expected to be connected by 2030. With such rapid growth, ensuring secure communication through SSH becomes increasingly important.
Basic SSH Setup for IoT Devices
Setting up SSH for IoT devices involves several steps:
- Enable SSH on the IoT device
- Configure the network settings
- Generate SSH keys for authentication
- Test the connection using an SSH client
For example, if you're setting up SSH on a Raspberry Pi, you would need to:
- Enable SSH in the Raspberry Pi configuration settings
- Install an SSH client like PuTTY on your computer
- Use the device's IP address to establish the connection
SSH Into IoT Device Example 1: Raspberry Pi
Raspberry Pi is a popular IoT device for hobbyists and professionals alike. Here's how you can use SSH to connect to a Raspberry Pi:
Step-by-Step Guide
- Power on the Raspberry Pi and connect it to your network
- Enable SSH by creating an empty file named "ssh" in the boot partition
- Find the IP address of the Raspberry Pi using a network scanning tool
- Open an SSH client and enter the command:
ssh pi@ - Enter the default password (usually "raspberry") when prompted
This example demonstrates the simplicity of SSH into IoT device configurations. With just a few steps, you can securely access and manage your Raspberry Pi remotely.
SSH Into IoT Device Example 2: ESP32
The ESP32 is a powerful IoT microcontroller with built-in Wi-Fi and Bluetooth capabilities. To use SSH with an ESP32, you'll need to:
Prerequisites
- Install the ESP32 SSH server firmware
- Configure the network settings on the ESP32
- Set up an SSH client on your computer
Once the setup is complete, you can connect to the ESP32 using the command:
ssh user@This example highlights the versatility of SSH in managing different types of IoT devices.
SSH Into IoT Device Example 3: Arduino
Arduino boards are widely used in IoT projects. While Arduino itself does not support SSH natively, you can connect it to a gateway device that supports SSH. For example:
Connecting Arduino via Raspberry Pi
- Set up SSH on the Raspberry Pi as described earlier
- Connect the Arduino to the Raspberry Pi using USB or serial communication
- Use SSH commands on the Raspberry Pi to interact with the Arduino
This setup allows you to leverage the strengths of both devices, combining the processing power of the Raspberry Pi with the flexibility of Arduino.
Security Best Practices for SSH
While SSH is inherently secure, following best practices ensures maximum protection:
- Use strong, unique passwords or SSH keys for authentication
- Disable password-based authentication and rely solely on SSH keys
- Regularly update the firmware and software on your IoT devices
- Limit SSH access to trusted IP addresses using firewall rules
According to a report by OWASP, weak authentication mechanisms are among the top vulnerabilities in IoT systems. Implementing these best practices can significantly reduce the risk of unauthorized access.
Troubleshooting Common SSH Issues
Even with proper setup, SSH connections can sometimes fail. Here are some common issues and their solutions:
Connection Timeout
- Verify the IP address and network settings
- Check for firewall or router restrictions
Authentication Failure
- Ensure the correct username and password are used
- Check the SSH key permissions and configurations
Troubleshooting SSH issues requires a systematic approach, starting with basic checks and moving to more advanced diagnostics if necessary.
Conclusion
In this comprehensive guide, we've explored the concept of SSH into IoT device examples, covering everything from basic setup to advanced troubleshooting techniques. SSH is a powerful tool for securely managing IoT devices, and understanding its capabilities is essential for anyone working in the IoT space.
Remember to:
- Follow best practices for SSH security
- Regularly update your devices and software
- Experiment with different examples to enhance your skills
We invite you to share your experiences and ask questions in the comments section below. Additionally, feel free to explore other articles on our site for more insights into IoT technology and secure communication protocols.


