Securely Connect Remote IoT VPC: Raspberry Pi Download Free Guide
In today's interconnected world, securely connecting remote IoT devices to a Virtual Private Cloud (VPC) using Raspberry Pi has become a crucial skill for developers and IT professionals. As more devices become part of the Internet of Things (IoT) ecosystem, ensuring secure communication and data privacy is paramount. This guide will provide you with comprehensive insights into setting up and managing remote IoT connections through a VPC using Raspberry Pi, with free downloadable resources to help you get started.
With the rapid advancement of technology, the demand for secure IoT solutions continues to grow. Businesses and individuals alike are seeking ways to protect their devices and networks from cyber threats while maintaining seamless connectivity. Understanding how to securely connect remote IoT devices using Raspberry Pi is not only a valuable skill but also a necessity in the modern digital landscape.
This article will walk you through the essential steps, tools, and best practices for setting up secure IoT VPC connections with Raspberry Pi. Whether you're a beginner or an experienced developer, you'll find actionable tips and expert advice to help you achieve your goals. Let's dive in and explore how you can enhance your IoT security with this powerful setup.
Overview of Secure IoT VPC Connections
Connecting IoT devices to a Virtual Private Cloud (VPC) ensures that your data remains secure while allowing remote access when needed. A VPC acts as a private network within the cloud, isolating your devices from public internet traffic and reducing the risk of unauthorized access. This setup is particularly beneficial for businesses that rely on IoT for operations, such as smart homes, industrial automation, and healthcare monitoring systems.
What is a VPC?
A Virtual Private Cloud (VPC) is a logically isolated section of a cloud provider's infrastructure. It allows users to define their own subnets, IP address ranges, and routing tables, providing a secure environment for hosting applications and services. By leveraging a VPC, you can control who has access to your IoT devices and how they communicate with each other.
Why is Security Important for IoT Devices?
IoT devices are often targeted by hackers due to their potential vulnerabilities. Without proper security measures, these devices can be exploited to gain access to sensitive information or disrupt critical systems. Securing IoT devices through a VPC not only protects your data but also ensures compliance with industry standards and regulations.
Why Use Raspberry Pi for IoT Security?
Raspberry Pi is a versatile and cost-effective platform for developing IoT applications. Its small form factor, low power consumption, and extensive community support make it an ideal choice for setting up secure IoT VPC connections. Additionally, Raspberry Pi offers a wide range of software options and libraries that simplify the development process.
Key Features of Raspberry Pi
- Compact size and lightweight design
- Multiple GPIO pins for connecting sensors and actuators
- Support for various operating systems, including Linux-based distributions
- Community-driven support and extensive documentation
Setting Up a VPC for IoT Devices
Setting up a VPC for IoT devices involves several steps, including defining subnets, configuring security groups, and establishing network access rules. Below is a step-by-step guide to help you create a secure VPC environment for your IoT devices.
Step 1: Define Subnets
Create separate subnets for different types of devices or applications. For example, you might have one subnet for sensors and another for actuators. This segmentation helps improve security by limiting communication between devices that don't need to interact.
Step 2: Configure Security Groups
Security groups act as virtual firewalls for your VPC. Use them to specify which inbound and outbound traffic is allowed. For instance, you can allow only HTTPS traffic from specific IP addresses to access your IoT devices.
Step 3: Set Up Network Access Rules
Define rules that govern how devices within your VPC can communicate with each other and the outside world. This includes specifying which ports are open and which protocols are permitted.
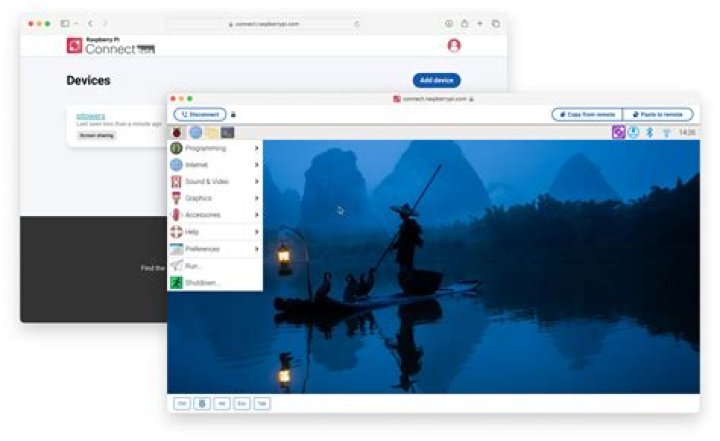
Establishing Secure Remote Connections
Once your VPC is set up, you'll need to establish secure remote connections to your IoT devices. This can be achieved using protocols such as SSH (Secure Shell) or SSL/TLS (Secure Sockets Layer/Transport Layer Security).
Using SSH for Remote Access
SSH is a widely used protocol for secure remote access. It encrypts all data transmitted between your device and the remote server, ensuring that sensitive information remains protected. To use SSH with Raspberry Pi:
- Install an SSH server on your Raspberry Pi
- Generate and configure SSH keys for authentication
- Connect to your Raspberry Pi from a remote machine using an SSH client
Implementing SSL/TLS
SSL/TLS provides end-to-end encryption for data transmitted between IoT devices and servers. This is particularly important for applications that handle sensitive information, such as financial transactions or healthcare data. To implement SSL/TLS:
- Obtain a digital certificate from a trusted Certificate Authority (CA)
- Install the certificate on your server or device
- Configure your application to use SSL/TLS for communication
Implementing Encryption for IoT Devices
Encryption is a critical component of IoT security. It ensures that even if data is intercepted, it cannot be read without the proper decryption key. There are several encryption methods you can use for IoT devices, including AES (Advanced Encryption Standard) and RSA (Rivest-Shamir-Adleman).
Choosing the Right Encryption Method
Selecting the appropriate encryption method depends on your specific requirements and constraints. For example, AES is commonly used for symmetric encryption due to its speed and efficiency, while RSA is preferred for asymmetric encryption when secure key exchange is necessary.
Best Practices for Encryption
- Use strong encryption algorithms and key lengths
- Regularly update encryption keys and certificates
- Implement secure key management practices
Essential Tools and Software
Several tools and software can assist you in setting up secure IoT VPC connections with Raspberry Pi. Below are some of the most popular options:
1. AWS IoT Core
AWS IoT Core is a managed cloud service that allows you to securely connect, monitor, and manage IoT devices at scale. It provides features such as device authentication, data encryption, and rule-based routing.
2. Mosquitto MQTT Broker
Mosquitto is an open-source message broker that implements the MQTT protocol. It enables lightweight communication between IoT devices and servers, making it ideal for resource-constrained environments.
3. Pi-hole
Pi-hole is a network-wide ad blocker that runs on Raspberry Pi. While primarily used for blocking ads, it can also enhance security by preventing malicious domains from being accessed.
Best Practices for IoT Security
Implementing best practices for IoT security can significantly reduce the risk of cyberattacks. Here are some key recommendations:
1. Regularly Update Firmware and Software
Keep your devices and software up to date with the latest security patches and updates. This helps protect against known vulnerabilities and exploits.
2. Use Strong Passwords and Authentication
Enforce the use of strong passwords and multi-factor authentication (MFA) for all devices and accounts. This adds an extra layer of security and makes it more difficult for attackers to gain unauthorized access.
3. Monitor and Audit Device Activity
Regularly monitor your IoT devices for unusual activity and audit logs to identify potential security threats. This allows you to take corrective action before any damage occurs.
Troubleshooting Common Issues
Despite careful planning and implementation, issues may arise when setting up secure IoT VPC connections. Below are some common problems and their solutions:
Problem: Unable to Connect to VPC
Solution: Verify that your VPC settings are correct and that all necessary security groups and network access rules are in place. Check for any misconfigurations or conflicts that may be preventing connectivity.
Problem: Slow Data Transfer
Solution: Optimize your network settings and ensure that your devices have sufficient bandwidth. Consider upgrading your hardware or using a more efficient communication protocol if necessary.
Free Downloads and Resources
To help you get started with securely connecting remote IoT VPC using Raspberry Pi, we've compiled a list of free downloads and resources:
Conclusion and Next Steps
In conclusion, securely connecting remote IoT devices to a VPC using Raspberry Pi is a powerful way to enhance your IoT security. By following the steps and best practices outlined in this guide, you can create a robust and reliable setup that meets your specific needs. Remember to regularly update your systems and monitor your devices for any potential threats.
We encourage you to take action by downloading the provided resources and experimenting with the tools and techniques discussed in this article. Feel free to leave a comment or share your experiences with the community. For more in-depth information, explore our other articles on IoT security and related topics.


