Securely Connect Remote IoT VPC: A Comprehensive Guide
Connecting remote IoT devices to a Virtual Private Cloud (VPC) securely is one of the most critical aspects of modern cloud computing infrastructure. As more businesses adopt IoT solutions, ensuring secure communication between devices and cloud networks becomes increasingly important. In this article, we will explore how to securely connect remote IoT devices to VPC and provide practical strategies to protect your data.
IoT technology has revolutionized industries, enabling smarter and more efficient operations. However, with the rise in connectivity comes the need for robust security measures. A secure connection ensures that sensitive information remains protected from unauthorized access and potential cyber threats.
This guide will walk you through the essential steps to establish a secure connection for remote IoT devices in a VPC environment. By the end of this article, you'll have a clear understanding of the best practices and tools available to safeguard your IoT ecosystem.
Overview of Securely Connect Remote IoT VPC
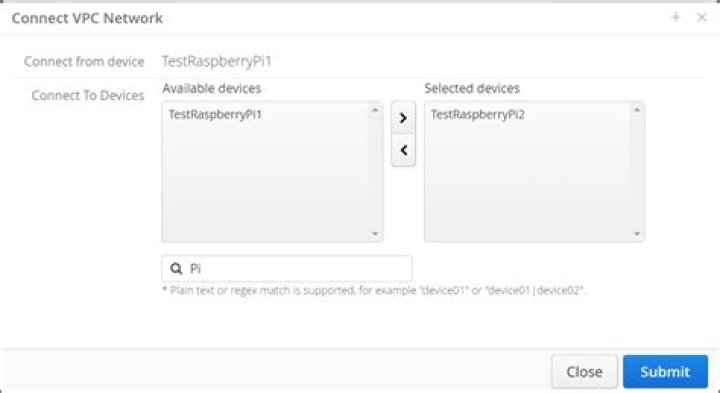
When it comes to securely connect remote IoT VPC, understanding the fundamental concepts is crucial. A Virtual Private Cloud (VPC) serves as a secure and isolated environment for hosting cloud resources. By integrating IoT devices into this setup, businesses can enhance their operational efficiency while maintaining data integrity.
Connecting IoT devices to a VPC requires careful planning and implementation. The process involves setting up secure communication channels, configuring firewalls, and implementing encryption protocols. These steps are essential to prevent unauthorized access and ensure data privacy.
In addition to technical considerations, organizations must also address regulatory compliance requirements. This includes adhering to industry standards such as GDPR, HIPAA, or ISO 27001, depending on the nature of their operations.
Understanding the Basics of VPC
What is a VPC?
A Virtual Private Cloud (VPC) is a logically isolated section of the cloud where an organization can deploy its resources. It provides a secure and scalable environment for hosting applications and storing data. VPCs are customizable, allowing users to define IP address ranges, create subnets, and configure routing tables.
Key Features of VPC
- Isolation: VPCs operate in a separate network space, ensuring that resources are protected from external interference.
- Flexibility: Users can configure VPC settings to meet their specific requirements, including defining security groups and access control lists.
- Scalability: VPCs can be easily expanded to accommodate growing business needs without compromising performance.
IoT Security Challenges and Solutions
IoT devices present unique security challenges due to their diverse functionalities and widespread deployment. Some common issues include weak authentication mechanisms, unencrypted data transmission, and outdated firmware. To address these concerns, organizations must adopt comprehensive security strategies.
Solutions such as implementing strong encryption protocols, enforcing multi-factor authentication, and regularly updating device firmware can significantly enhance IoT security. Additionally, employing network segmentation techniques can limit potential damage in case of a breach.
Designing a Secure Network Architecture
Best Practices for Network Design
Creating a secure network architecture involves several key steps. First, organizations should define clear access policies and enforce them through security groups and network access control lists (NACLs). This ensures that only authorized devices and users can interact with the VPC.
Another important aspect is setting up a demilitarized zone (DMZ) to isolate IoT devices from the core network. This approach reduces the risk of lateral movement in case of a successful attack.
Tools for Network Design
- CloudFormation: A service provided by AWS that allows users to automate the creation of VPCs and related resources.
- Terraform: An open-source infrastructure as code tool that supports multiple cloud platforms, enabling consistent network configurations.
Encryption Methods for IoT Devices
Encryption plays a vital role in securing data transmitted between IoT devices and VPCs. By encrypting data at rest and in transit, organizations can protect sensitive information from interception and unauthorized access.
Some widely used encryption methods include Advanced Encryption Standard (AES), Transport Layer Security (TLS), and Secure Sockets Layer (SSL). Each method has its own strengths and is suitable for different use cases. For instance, AES is commonly used for encrypting data at rest, while TLS and SSL are ideal for securing data in transit.
Authentication Protocols for IoT Devices
Authentication ensures that only legitimate devices and users can access the VPC. Implementing robust authentication protocols is essential for maintaining the security of IoT ecosystems.
Popular authentication methods include:
- OAuth 2.0: An authorization framework that enables third-party applications to access resources on behalf of users.
- JSON Web Tokens (JWT): A compact and self-contained way to transmit information between parties as a JSON object.
- Biometric Authentication: Utilizing unique biological characteristics, such as fingerprints or facial recognition, to verify identity.
Monitoring and Managing IoT Connections
Importance of Monitoring
Continuous monitoring of IoT connections is crucial for detecting and responding to potential security threats. By implementing real-time monitoring solutions, organizations can quickly identify anomalies and take corrective actions.
Tools for Monitoring
- Amazon CloudWatch: A monitoring service provided by AWS that offers insights into resource utilization and performance metrics.
- Splunk: A data analytics platform that helps organizations analyze and visualize machine-generated data, including IoT traffic.
Best Practices for Secure IoT VPC Connections
To ensure the security of IoT devices connected to a VPC, organizations should follow these best practices:
- Regularly update device firmware and software to patch vulnerabilities.
- Implement strong password policies and enforce multi-factor authentication.
- Segment the network to limit the impact of potential breaches.
- Monitor traffic patterns and investigate unusual activities.
Tools and Technologies for Secure Connections
Several tools and technologies are available to facilitate secure connections between IoT devices and VPCs. These include:
- AWS IoT Core: A managed cloud service that enables secure communication between IoT devices and cloud applications.
- Microsoft Azure IoT Hub: A cloud-based solution that provides reliable messaging and device management capabilities.
Future Trends in IoT Security
As IoT technology continues to evolve, new security trends are emerging. These include the adoption of blockchain for secure data sharing, the use of artificial intelligence for threat detection, and the development of quantum-resistant encryption algorithms.
Organizations must stay informed about these developments to maintain the security of their IoT ecosystems. By embracing innovative solutions and adhering to industry best practices, businesses can protect their assets and ensure long-term success.
Conclusion
In conclusion, securely connecting remote IoT devices to a VPC requires a combination of technical expertise, strategic planning, and adherence to security best practices. By understanding the challenges and implementing appropriate solutions, organizations can create a robust and secure IoT infrastructure.
We encourage readers to leave comments, share this article, and explore other resources on our website to deepen their knowledge of IoT security. Together, we can build a safer and more connected world.