Securely Connect Remote IoT P2P SSH Android: A Comprehensive Guide
In today's interconnected world, securely connect remote IoT P2P SSH Android has become a crucial aspect of modern technology. As more devices become part of the Internet of Things (IoT), ensuring secure connections is paramount to safeguard sensitive data and maintain privacy. Whether you're a developer, system administrator, or tech enthusiast, understanding how to secure remote IoT connections using P2P SSH on Android is essential.
With billions of IoT devices now in use globally, the risks associated with unsecured connections are significant. Cyber threats such as unauthorized access, data breaches, and malware attacks are growing concerns that need immediate attention. This article will delve into the intricacies of setting up a secure IoT environment using peer-to-peer (P2P) SSH connections on Android devices.
Our focus will be on providing actionable insights and practical steps to help you achieve robust security measures. By the end of this guide, you'll have the knowledge and tools necessary to implement secure IoT connections effectively. Let’s get started by exploring the fundamentals and advanced techniques involved in this process.
Understanding the Basics of Secure IoT Connections
Before diving into the technical aspects, it's essential to understand the foundation of secure IoT connections. Securely connect remote IoT P2P SSH Android involves several key components that work together to ensure data protection and device security.
IoT devices rely heavily on communication protocols to exchange information. Among these protocols, SSH (Secure Shell) stands out as one of the most secure methods for remote access and communication. SSH provides encryption for data transmission, authentication mechanisms, and secure command execution, making it an ideal choice for IoT applications.
What is SSH and Why is It Important?
SSH, or Secure Shell, is a cryptographic network protocol designed for secure communication over unsecured networks. It is widely used for remote command-line login and other secure network services. SSH offers several advantages, including:
- Encryption: Protects data during transmission.
- Authentication: Ensures only authorized users can access the system.
- Integrity: Guarantees that data has not been tampered with during transmission.
Peer-to-Peer (P2P) Connections in IoT
Peer-to-Peer (P2P) connections are a decentralized approach to networking where devices communicate directly with each other without relying on a central server. In the context of IoT, P2P connections offer several benefits:
- Reduced latency: Faster communication between devices.
- Lower bandwidth usage: Minimizes reliance on central servers.
- Improved scalability: Easily accommodates a growing number of devices.
However, securing P2P connections in IoT requires careful planning and implementation to prevent unauthorized access and data breaches.
Challenges in Securing P2P IoT Connections
While P2P connections offer numerous advantages, they also pose unique security challenges. Some of the key challenges include:
- Device authentication: Ensuring only legitimate devices can participate in the network.
- Data encryption: Protecting sensitive information during transmission.
- Intrusion detection: Monitoring the network for suspicious activities.
Setting Up SSH on Android Devices
Android devices are increasingly being used as control points for IoT systems. Setting up SSH on Android involves installing an SSH client or server application and configuring it to work with your IoT devices. Below are the steps to set up SSH on Android:
Step 1: Install an SSH Client
There are several SSH client applications available on the Google Play Store. Some popular options include:
- Termius
- Server Ultimate
- ConnectBot
Choose a reliable app that suits your needs and install it on your Android device.
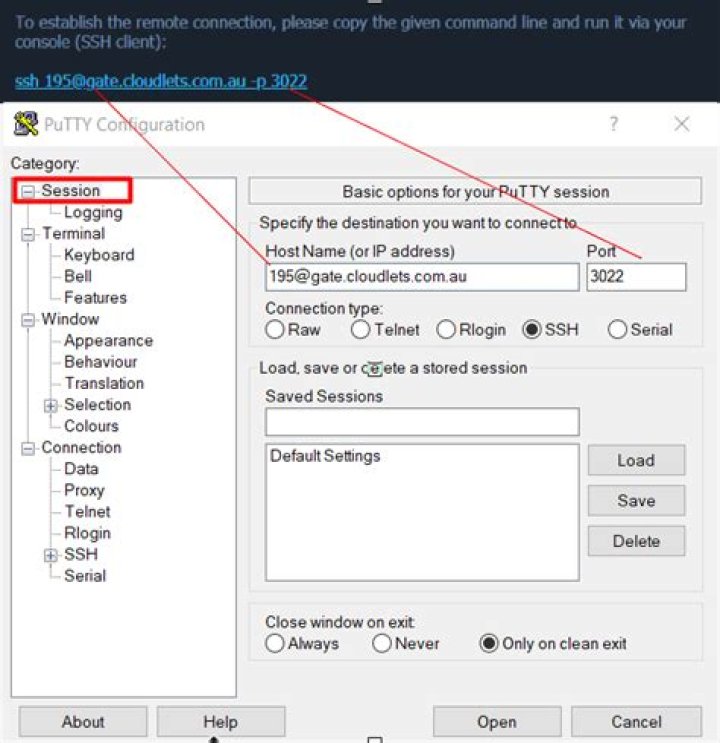
Step 2: Configure SSH Settings
Once the SSH client is installed, configure the settings to connect to your IoT devices. This typically involves:
- Specifying the IP address or hostname of the remote device.
- Setting the port number (default is 22 for SSH).
- Entering the username and password or using SSH keys for authentication.
Implementing Secure IoT P2P SSH Connections
Implementing secure IoT P2P SSH connections requires a combination of best practices and advanced techniques. Below are some strategies to enhance the security of your IoT network:
1. Use Strong Authentication
Strong authentication is the first line of defense in securing IoT connections. Consider using:
- SSH keys: Generate unique public and private keys for each device.
- MFA (Multi-Factor Authentication): Add an extra layer of security by requiring multiple forms of verification.
2. Encrypt All Data
Data encryption ensures that even if data is intercepted, it cannot be read by unauthorized parties. Use strong encryption algorithms such as AES-256 to protect your data.
3. Regularly Update Firmware
Keep your IoT devices and Android devices up to date with the latest firmware and security patches. This helps protect against known vulnerabilities and exploits.
Best Practices for Securing IoT Networks
Adopting best practices is crucial for maintaining the security of your IoT network. Below are some recommendations:
- Segment your network to isolate IoT devices from other systems.
- Monitor network traffic for suspicious activities using intrusion detection systems (IDS).
- Limit access to IoT devices to only authorized personnel.
Tools for Monitoring IoT Security
Several tools are available to help monitor and manage IoT security. Some popular options include:
- Snort: An open-source intrusion detection system.
- Wireshark: A network protocol analyzer for capturing and analyzing network traffic.
- OpenVAS: A vulnerability scanning tool for identifying security weaknesses.
Advanced Techniques for Secure IoT Connections
For those seeking an extra level of security, advanced techniques such as blockchain and zero-trust architecture can be implemented. These methods provide robust protection against cyber threats and ensure the integrity of IoT communications.
Blockchain for IoT Security
Blockchain technology offers a decentralized and tamper-proof method for securing IoT connections. By storing transaction records in a distributed ledger, blockchain ensures that data cannot be altered without detection.
Zero-Trust Architecture
Zero-trust architecture assumes that no device or user can be trusted by default. It requires continuous verification and authentication for all connections, significantly reducing the risk of unauthorized access.
Data and Statistics on IoT Security
According to a report by Gartner, the global IoT security market is expected to reach $3.1 billion by 2023. The same report highlights that 20% of organizations will experience an IoT-related security breach by 2025. These statistics underscore the importance of implementing robust security measures for IoT devices.
Key Findings from Recent Studies
Recent studies have shown that:
- Over 70% of IoT devices lack basic security features.
- Unsecured IoT devices are responsible for 30% of all data breaches.
- 50% of organizations do not have a dedicated IoT security strategy.
Conclusion
Securely connect remote IoT P2P SSH Android is a critical component of modern technology. By understanding the basics of SSH, implementing P2P connections, and adopting best practices, you can significantly enhance the security of your IoT network. Remember to regularly update your systems, use strong authentication methods, and monitor your network for potential threats.
We invite you to share your thoughts and experiences in the comments section below. Additionally, feel free to explore other articles on our website for more insights into IoT security and related topics. Together, let's build a safer and more secure digital future.


