Secure SSH Access for IoT Devices: A Comprehensive Guide
With the rapid growth of IoT devices, securing SSH access has become a critical aspect of maintaining network integrity and protecting sensitive data. IoT devices are increasingly becoming an integral part of daily life, from smart home appliances to industrial automation systems. However, as these devices become more interconnected, they also become potential targets for cyber threats. Understanding how to secure SSH access for IoT devices is essential to safeguarding your network infrastructure.
The importance of SSH (Secure Shell) in the context of IoT cannot be overstated. SSH is a cryptographic protocol designed to provide secure communication over unsecured networks. For IoT devices, which often operate in environments where physical security is minimal, SSH acts as a robust barrier against unauthorized access and data breaches. This article aims to provide a detailed exploration of SSH access for IoT devices, offering practical guidance and best practices.
Whether you are a network administrator, IT professional, or simply someone interested in IoT security, this guide will equip you with the knowledge needed to implement secure SSH configurations. By following the steps outlined here, you can significantly enhance the security of your IoT devices and protect your network from potential threats.
Introduction to SSH
SSH, or Secure Shell, is a network protocol that facilitates secure communication between devices over an unsecured network. Originally developed in 1995 as a replacement for less secure protocols like Telnet and rlogin, SSH has become the standard for remote access and command execution. It uses encryption to protect data in transit, ensuring that sensitive information remains confidential and tamper-proof.
SSH operates on a client-server model, where the client initiates a connection to the server, and authentication is performed using either passwords or cryptographic keys. The protocol supports various encryption algorithms, including AES, RSA, and ECDSA, making it versatile and adaptable to different security requirements.
For IoT devices, SSH provides a reliable method for remote management and configuration. Devices can be accessed securely from anywhere in the world, allowing administrators to perform updates, troubleshoot issues, and monitor performance without compromising security.
IoT Security Challenges
The proliferation of IoT devices has introduced new security challenges that must be addressed to ensure the safety and integrity of networks. Unlike traditional computing devices, IoT devices often lack robust security features due to their limited processing power and memory. This makes them vulnerable to attacks such as:
- Brute Force Attacks: Hackers attempt to guess login credentials by systematically trying different combinations until they succeed.
- Man-in-the-Middle Attacks: Attackers intercept communication between devices, potentially altering or stealing data.
- Firmware Vulnerabilities: Many IoT devices run outdated firmware with known security flaws, making them easy targets for exploitation.
- Default Credentials: Devices often ship with default usernames and passwords, which are frequently left unchanged by users.
Addressing these challenges requires a proactive approach to security, including the implementation of secure protocols like SSH.
Why SSH is Important for IoT Devices
SSH plays a crucial role in securing IoT devices by providing a secure channel for communication and remote access. Here are some reasons why SSH is essential for IoT:
1. Data Encryption: SSH encrypts all data transmitted between devices, ensuring that sensitive information remains confidential and cannot be intercepted by attackers.
2. Strong Authentication: SSH supports multiple authentication methods, including password-based and public key authentication, allowing administrators to choose the most secure option for their environment.
3. Remote Management: With SSH, administrators can remotely manage and configure IoT devices, reducing the need for physical access and minimizing downtime.
4. Auditability: SSH logs all connections and activities, providing a valuable record for auditing and troubleshooting purposes.
Secure SSH Configuration for IoT
Configuring SSH securely is essential to protecting IoT devices from potential threats. Below are some best practices for setting up SSH on IoT devices:
- Disable Password Authentication: Use public key authentication instead of passwords to eliminate the risk of brute force attacks.
- Change Default Ports: Avoid using the default SSH port (22) to reduce the likelihood of automated attacks.
- Limit Access: Restrict SSH access to specific IP addresses or subnets to prevent unauthorized connections.
- Enable Two-Factor Authentication: Add an extra layer of security by requiring users to provide a second form of verification.
By following these guidelines, you can significantly enhance the security of your SSH implementation and protect your IoT devices from potential threats.
Common SSH Vulnerabilities in IoT
Despite its robust security features, SSH is not immune to vulnerabilities. Some common issues that can affect SSH in IoT environments include:
- Weak Keys: Using weak or improperly generated cryptographic keys can compromise the security of SSH connections.
- Outdated Software: Running outdated versions of SSH software can expose devices to known vulnerabilities.
- Improper Configuration: Misconfigurations, such as leaving default settings unchanged, can create security loopholes.
- Insufficient Logging: Failing to properly configure logging can make it difficult to detect and respond to security incidents.
Regularly updating software, generating strong keys, and carefully configuring SSH settings are essential steps in mitigating these vulnerabilities.
Best Practices for SSH Access in IoT
To ensure the highest level of security for SSH access in IoT environments, consider implementing the following best practices:
1. Regular Updates: Keep SSH software up to date with the latest security patches and improvements.
2. Key Management: Establish a robust key management policy to ensure that cryptographic keys are properly generated, stored, and rotated.
3. Network Segmentation: Isolate IoT devices on separate networks to limit the potential impact of a security breach.
4. Monitoring and Auditing: Continuously monitor SSH activity and regularly review logs to detect and respond to suspicious behavior.
Tools for SSH Management in IoT
Several tools are available to help manage SSH access in IoT environments. These tools can simplify key management, automate updates, and provide valuable insights into network activity. Some popular options include:
- OpenSSH: A widely used open-source SSH implementation that provides robust security features.
- KeyCDN: A tool for managing SSH keys and certificates, offering centralized control and automated updates.
- Ansible: A configuration management tool that can automate SSH setup and management across multiple devices.
By leveraging these tools, administrators can streamline SSH management and improve the overall security of their IoT infrastructure.
SSH Automation for IoT Devices
Automation plays a critical role in managing SSH access for large-scale IoT deployments. Automating tasks such as key generation, distribution, and rotation can significantly reduce the administrative burden and minimize the risk of human error. Some common automation techniques include:
- Scripting: Writing custom scripts to automate repetitive SSH tasks, such as user provisioning and key management.
- Configuration Management: Using tools like Puppet or Chef to enforce consistent SSH configurations across all devices.
- Orchestration Platforms: Employing platforms like Kubernetes to manage SSH access in complex, distributed environments.
Automation not only improves efficiency but also enhances security by ensuring that best practices are consistently applied across all devices.
Case Studies: Real-World Applications
Several organizations have successfully implemented SSH access for IoT devices, demonstrating its effectiveness in real-world scenarios. For example:
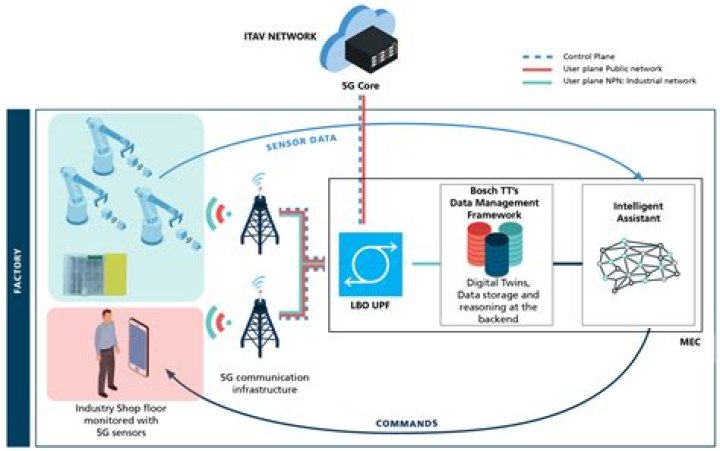
Case Study 1: A smart city initiative used SSH to securely manage thousands of IoT devices, including traffic lights, parking sensors, and environmental monitors. By implementing robust SSH configurations and automation tools, they were able to maintain high levels of security while minimizing administrative overhead.
Case Study 2: A manufacturing company deployed SSH to secure remote access to industrial IoT devices on their factory floor. This allowed engineers to perform diagnostics and updates without the need for physical access, improving efficiency and reducing downtime.
The Future of SSH in IoT
As IoT continues to evolve, the role of SSH in securing device communication is likely to grow. Emerging technologies, such as quantum computing and blockchain, may introduce new challenges and opportunities for SSH in IoT environments. Additionally, advancements in machine learning and artificial intelligence could enhance SSH automation and threat detection capabilities.
Staying informed about these developments and adapting security strategies accordingly will be essential for maintaining the security of IoT devices in the future.
Conclusion
Securing SSH access for IoT devices is a critical component of maintaining network security and protecting sensitive data. By understanding the challenges and implementing best practices, administrators can significantly enhance the security of their IoT infrastructure. This guide has provided a comprehensive overview of SSH in the context of IoT, covering topics such as secure configuration, common vulnerabilities, and automation techniques.
We encourage readers to apply the knowledge gained from this article to their own environments and to continue exploring new developments in IoT security. Please feel free to leave comments, share this article, or explore other resources on our site for more information on securing your IoT devices.