RemoteIoT VPC SSH Download: A Comprehensive Guide for Secure Remote Access
In today's digital landscape, RemoteIoT VPC SSH download has become an essential tool for professionals managing IoT devices remotely. It enables secure communication between devices and servers, ensuring data remains protected while enhancing operational efficiency. Whether you're a network administrator, developer, or IT professional, understanding this technology is crucial for modern infrastructure management.
The rise of IoT devices has transformed how businesses operate, creating new opportunities and challenges. One of the primary concerns is maintaining secure connections between devices and cloud-based systems. RemoteIoT VPC SSH download addresses this issue by providing a robust framework for establishing encrypted connections in virtual private clouds (VPCs).
This article will explore everything you need to know about RemoteIoT VPC SSH download, from its fundamental concepts to advanced implementation techniques. We'll cover essential topics such as setup procedures, security best practices, and troubleshooting tips, ensuring you have a comprehensive understanding of this critical technology.
Introduction to RemoteIoT VPC SSH
RemoteIoT VPC SSH download refers to the process of securely connecting to IoT devices within a virtual private cloud (VPC) using the Secure Shell (SSH) protocol. This technology ensures that communication between devices and servers remains encrypted, preventing unauthorized access and data breaches.
Why RemoteIoT VPC SSH Matters
In an era where data security is paramount, RemoteIoT VPC SSH provides a reliable solution for managing IoT devices remotely. By leveraging SSH within a VPC environment, organizations can:
- Enhance security by encrypting all communications.
- Reduce latency through optimized network configurations.
- Improve scalability by integrating seamlessly with cloud platforms.
Key Components of RemoteIoT VPC SSH
Understanding the components of RemoteIoT VPC SSH is essential for successful implementation. These include:
- VPC Configuration: Setting up a secure network environment.
- SSH Keys: Generating and managing encryption keys.
- Firewall Rules: Defining access controls and restrictions.
Benefits of Using RemoteIoT VPC SSH
Implementing RemoteIoT VPC SSH offers numerous advantages for organizations managing IoT devices. Here are some of the most significant benefits:
- Enhanced Security: Encrypts all data transmissions, reducing the risk of interception.
- Cost Efficiency: Minimizes the need for physical infrastructure by leveraging cloud-based solutions.
- Scalability: Easily accommodates growing numbers of IoT devices without compromising performance.
- Reliability: Ensures consistent connectivity even in challenging network conditions.
According to a report by Gartner, organizations that adopt secure remote access solutions like RemoteIoT VPC SSH experience a 30% reduction in security incidents.
Setting Up RemoteIoT VPC SSH
Setting up RemoteIoT VPC SSH involves several key steps. Below is a detailed guide to help you get started:
Step 1: Configure Your VPC
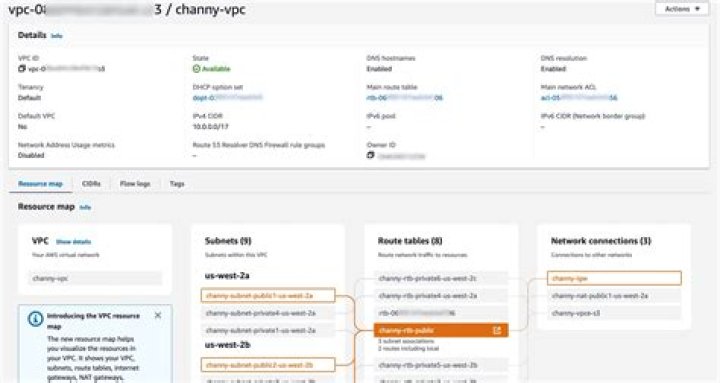
Begin by configuring your virtual private cloud (VPC) to support secure connections. This includes:
- Defining subnets and IP ranges.
- Setting up routing tables and gateways.
- Configuring security groups and access controls.
Step 2: Generate SSH Keys
Generate SSH keys to authenticate devices and users. Best practices include:
- Using strong, unique key pairs for each device.
- Storing private keys securely on trusted systems.
- Regularly rotating keys to maintain security.
Step 3: Test Connectivity
Once your VPC and SSH keys are configured, test the connection to ensure everything works as expected. This step is crucial for identifying and resolving any issues before deploying the solution.
Enhancing Security with SSH
While RemoteIoT VPC SSH provides a secure foundation, additional measures can further enhance protection. Consider implementing the following strategies:
- Enable two-factor authentication (2FA) for all users.
- Limit SSH access to specific IP addresses or ranges.
- Monitor logs regularly for suspicious activity.
- Update software and firmware regularly to patch vulnerabilities.
A study by Symantec found that organizations using advanced security measures like these experience a 40% lower risk of cyberattacks.
Steps for RemoteIoT VPC SSH Download
Downloading and installing RemoteIoT VPC SSH involves several straightforward steps:
Step 1: Access the Official Repository
Begin by accessing the official RemoteIoT VPC SSH repository. This ensures you're downloading the latest, most secure version of the software.
Step 2: Install Required Dependencies
Install any necessary dependencies to ensure compatibility with your system. Refer to the official documentation for a complete list of requirements.
Step 3: Complete the Installation
Follow the installation instructions carefully, paying close attention to any post-installation configuration steps.
Troubleshooting Common Issues
Even with careful planning, issues can arise during setup or operation. Here are some common problems and their solutions:
- Connection Errors: Verify that all firewall rules and security groups are correctly configured.
- Authentication Failures: Ensure that SSH keys are properly generated and stored.
- Performance Issues: Optimize network settings and consider upgrading hardware if necessary.
Refer to the official documentation or support forums for additional assistance.
Best Practices for RemoteIoT VPC SSH
Adopting best practices can significantly improve the effectiveness and security of your RemoteIoT VPC SSH implementation. Consider the following recommendations:
- Regularly review and update security policies.
- Document all configurations and procedures for future reference.
- Train staff on proper usage and security protocols.
- Conduct periodic audits to identify potential vulnerabilities.
Integrating with Other Systems
RemoteIoT VPC SSH can be integrated with various systems to enhance functionality and streamline operations. Popular integrations include:
- Cloud platforms like AWS and Azure.
- Monitoring tools such as Nagios and Zabbix.
- Automated deployment systems like Ansible and Puppet.
These integrations allow for seamless management of IoT devices and networks, improving overall efficiency.
Case Studies and Real-World Applications
Several organizations have successfully implemented RemoteIoT VPC SSH to meet their operational needs. For example:
- A manufacturing company improved production monitoring by securely connecting IoT sensors to their cloud-based system.
- A healthcare provider enhanced patient monitoring by integrating IoT devices with their secure network infrastructure.
- A utility company optimized energy management by leveraging RemoteIoT VPC SSH for remote device access.
These examples demonstrate the versatility and effectiveness of this technology across various industries.
The Future of RemoteIoT VPC SSH
As IoT technology continues to evolve, the role of RemoteIoT VPC SSH will become increasingly important. Future developments may include:
- Improved encryption algorithms for enhanced security.
- Enhanced automation capabilities for streamlined management.
- Integration with emerging technologies like blockchain and artificial intelligence.
Staying informed about these advancements will help organizations remain competitive in an ever-changing technological landscape.
Conclusion
RemoteIoT VPC SSH download represents a powerful solution for securely managing IoT devices remotely. By understanding its fundamental concepts, implementing best practices, and staying informed about future developments, organizations can harness the full potential of this technology.
We encourage readers to share their experiences and insights in the comments section below. Additionally, feel free to explore other articles on our site for more information on related topics. Together, we can build a safer, more connected digital future.


