RemoteIoT SSH Example: A Comprehensive Guide to Secure Remote Access
In today's interconnected world, remote IoT (Internet of Things) management is becoming increasingly important. As more devices are connected to the internet, secure remote access has become a critical aspect of maintaining and managing these devices. RemoteIoT SSH Example serves as a fundamental tool to ensure secure communication between devices and networks.
Whether you're a network administrator, developer, or enthusiast, understanding how to implement secure shell (SSH) protocols for remote IoT devices is essential. This guide will walk you through the basics of RemoteIoT SSH, its importance, and practical examples to help you secure your IoT ecosystem.
By the end of this article, you'll have a comprehensive understanding of RemoteIoT SSH, including its setup, configuration, and best practices to ensure your devices remain secure and functional.
Introduction to RemoteIoT SSH
RemoteIoT SSH is a protocol designed to facilitate secure remote access to IoT devices. It ensures encrypted communication between devices and servers, protecting sensitive data from unauthorized access. The SSH protocol uses cryptographic techniques to authenticate users and secure data transmission.
IoT devices often operate in diverse environments, making them vulnerable to cyber threats. With RemoteIoT SSH, you can establish a secure connection to manage and monitor these devices remotely, ensuring their functionality and security.
What Makes RemoteIoT SSH Unique?
Unlike traditional remote access methods, RemoteIoT SSH offers advanced features such as:
- End-to-end encryption
- Two-factor authentication
- Support for multiple users
- Customizable configurations
Why Use RemoteIoT SSH?
Using RemoteIoT SSH provides numerous advantages for managing IoT devices. It ensures that data transmitted between devices and servers remains confidential and tamper-proof. Additionally, it simplifies the management of IoT ecosystems by offering a centralized platform for remote access.
Key Benefits of RemoteIoT SSH
- Security: Protects against unauthorized access and cyberattacks.
- Efficiency: Enables remote troubleshooting and maintenance.
- Scalability: Supports a growing number of IoT devices.
How RemoteIoT SSH Works
The RemoteIoT SSH protocol operates by establishing a secure connection between a client (user) and a server (IoT device). This process involves several steps:
- Authentication: The client verifies its identity using credentials or public key authentication.
- Encryption: Data transmitted between the client and server is encrypted to prevent interception.
- Session Management: A secure session is maintained throughout the connection, ensuring uninterrupted communication.
Setting Up RemoteIoT SSH
Setting up RemoteIoT SSH involves configuring both the client and server environments. Below are the steps to follow:
Step 1: Install SSH on Your IoT Device
Most IoT devices come with SSH pre-installed. If not, you can install it using the following command:
sudo apt-get install openssh-server
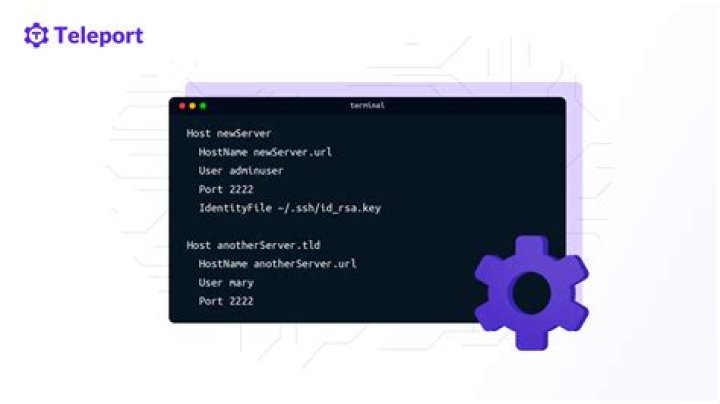
Step 2: Configure SSH Settings
Edit the SSH configuration file to customize settings such as port numbers and authentication methods:
sudo nano /etc/ssh/sshd_config
Step 3: Restart SSH Service
After making changes, restart the SSH service to apply the new settings:
sudo systemctl restart ssh
Common RemoteIoT SSH Commands
Here are some frequently used SSH commands for managing IoT devices:
ssh username@hostname: Connect to an IoT device.scp file.txt username@hostname:/path/to/destination: Transfer files securely.ssh-keygen: Generate public and private keys for authentication.
Securing Your RemoteIoT SSH
While RemoteIoT SSH is inherently secure, additional measures can enhance its protection:
Enable Two-Factor Authentication
Two-factor authentication adds an extra layer of security by requiring users to provide a second form of verification, such as a one-time password (OTP).
Use Strong Passwords
Ensure that all user accounts have strong, complex passwords to prevent brute-force attacks.
Troubleshooting RemoteIoT SSH
Even with proper setup, issues may arise when using RemoteIoT SSH. Below are some common problems and their solutions:
Connection Refused
If you encounter a "connection refused" error, verify that the SSH service is running on the IoT device:
sudo systemctl status ssh
Authentication Failed
Check your username, password, or key pair to ensure they are correct. Also, confirm that the SSH configuration file allows the chosen authentication method.
RemoteIoT SSH Best Practices
To maximize the security and efficiency of RemoteIoT SSH, follow these best practices:
- Regularly update SSH software to address vulnerabilities.
- Limit access to trusted users and IP addresses.
- Monitor SSH logs for suspicious activity.
Real-World RemoteIoT SSH Examples
Here are some practical examples of how RemoteIoT SSH is used in real-world scenarios:
Example 1: Smart Home Automation
RemoteIoT SSH enables homeowners to securely manage smart home devices, such as thermostats and lighting systems, from anywhere in the world.
Example 2: Industrial IoT
In industrial settings, RemoteIoT SSH is used to monitor and control machinery, ensuring optimal performance and minimizing downtime.
Conclusion and Next Steps
In conclusion, RemoteIoT SSH is a powerful tool for managing IoT devices securely and efficiently. By following the guidelines outlined in this article, you can implement SSH in your IoT ecosystem and protect your devices from potential threats.
We encourage you to explore further resources and share your experiences in the comments section below. For more insights into IoT security and management, check out our other articles on the website.