Monitor IoT Device Behind Router: A Comprehensive Guide to Boosting Your Network Security
In today's interconnected world, monitoring IoT devices behind a router has become an essential practice for maintaining network security. The proliferation of IoT devices has created new vulnerabilities that cybercriminals can exploit. By understanding how to effectively monitor these devices, you can protect your network from unauthorized access and potential cyberattacks.
As more households and businesses adopt smart devices, the risk of security breaches increases exponentially. It's crucial to recognize that IoT devices often lack robust security features, making them attractive targets for hackers. Therefore, learning how to monitor IoT devices behind a router is not just a technical skill but a necessity for safeguarding your digital environment.
This guide will delve into the importance of monitoring IoT devices, provide step-by-step instructions for setting up monitoring systems, and offer expert tips to enhance your network's security. By the end of this article, you'll have a comprehensive understanding of how to protect your IoT ecosystem effectively.
The Importance of Monitoring IoT Devices Behind Router
Monitoring IoT devices behind a router is vital for maintaining the integrity and security of your network. With the increasing number of smart devices, the potential for unauthorized access grows significantly. By implementing a robust monitoring system, you can detect suspicious activities and take immediate action to prevent data breaches.
Why Monitoring Matters
IoT devices often lack the advanced security features found in traditional computing devices. This makes them vulnerable to attacks such as malware infections, unauthorized access, and data theft. Regular monitoring allows you to:
- Identify unauthorized devices connected to your network.
- Monitor device activity and detect anomalies.
- Ensure that all devices are updated with the latest security patches.
- Prevent potential attacks by isolating compromised devices.
According to a report by Gartner, the number of IoT devices is expected to reach 25 billion by 2030, emphasizing the growing need for effective monitoring solutions.
Understanding the Risks of Unmonitored IoT Devices
Unmonitored IoT devices pose significant risks to both individuals and organizations. These devices can serve as entry points for cybercriminals to access sensitive data or disrupt network operations. Understanding these risks is the first step in protecting your network.
Common Security Threats
Some of the most common security threats associated with unmonitored IoT devices include:
- Botnets: Hackers can use compromised IoT devices to create botnets for launching DDoS attacks.
- Data Breaches: Vulnerable IoT devices can expose sensitive information, leading to data breaches.
- Unauthorized Access: Weak authentication mechanisms make it easier for attackers to gain unauthorized access.
A study by Symantec found that nearly 70% of IoT devices have significant security vulnerabilities, underscoring the importance of proactive monitoring.
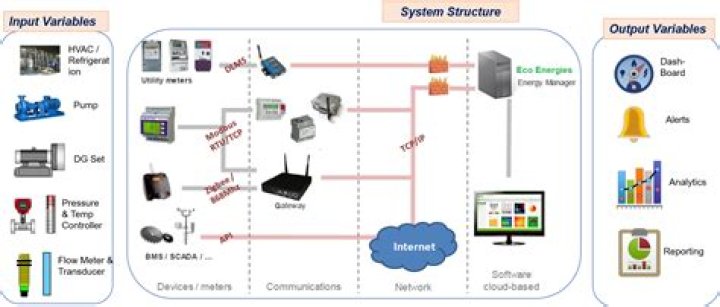
Tools for Monitoring IoT Devices
Several tools are available for monitoring IoT devices behind a router. These tools range from basic software applications to advanced hardware solutions, each offering unique features to enhance your network's security.
Popular Monitoring Tools
Here are some of the most widely used tools for IoT device monitoring:
- Wireshark: A network protocol analyzer that allows you to capture and analyze network traffic.
- Shodan: An IoT search engine that helps identify exposed devices on the internet.
- PRTG Network Monitor: A comprehensive monitoring solution that provides real-time insights into network activity.
These tools empower users to gain visibility into their IoT ecosystems and take proactive measures to secure their networks.
Setting Up a Monitoring System
Setting up a monitoring system for IoT devices behind a router involves several steps. By following these steps, you can establish a robust monitoring framework that ensures the security of your network.
Step-by-Step Guide
Here's a step-by-step guide to setting up your monitoring system:
- Identify Devices: Create a list of all IoT devices connected to your network.
- Install Monitoring Software: Choose and install a suitable monitoring tool based on your needs.
- Configure Alerts: Set up alerts for unusual activities or unauthorized access attempts.
- Regularly Review Logs: Analyze logs to identify potential security threats.
By following these steps, you can create a secure environment for your IoT devices and protect your network from potential threats.
Enhancing IoT Device Security
Beyond monitoring, enhancing the security of IoT devices is essential for maintaining a secure network. Implementing best practices in device management can significantly reduce the risk of cyberattacks.
Security Best Practices
Consider implementing the following security best practices:
- Regular Updates: Ensure all devices are updated with the latest firmware and security patches.
- Strong Passwords: Use strong, unique passwords for each device and change them regularly.
- Network Segmentation: Isolate IoT devices on a separate network to limit potential damage in case of a breach.
Implementing these practices not only enhances security but also improves the overall performance of your IoT ecosystem.
Optimizing Network Security
Optimizing network security involves a combination of hardware and software solutions. By integrating these solutions, you can create a multi-layered defense system that protects your network from various threats.
Key Strategies for Network Optimization
Here are some key strategies for optimizing network security:
- Firewall Configuration: Configure your firewall to block unauthorized access and filter out malicious traffic.
- Intrusion Detection Systems: Deploy intrusion detection systems to monitor network traffic for suspicious activities.
- Encryption: Use encryption protocols to secure data transmitted between devices and the router.
These strategies ensure that your network remains secure and resilient against potential threats.
Automation in IoT Device Monitoring
Automation plays a crucial role in IoT device monitoring by reducing the burden on administrators and improving response times. By automating routine tasks, you can focus on more critical aspects of network management.
Benefits of Automation
The benefits of automation in IoT device monitoring include:
- Real-Time Alerts: Automated systems can send real-time alerts for suspicious activities.
- Efficient Resource Management: Automation helps optimize resource usage by automating routine tasks.
- Improved Accuracy: Automated systems reduce the risk of human error in monitoring processes.
Leveraging automation in your monitoring system can significantly enhance the security and efficiency of your IoT ecosystem.
Troubleshooting Common Issues
Despite the best efforts, issues may arise in IoT device monitoring. Understanding how to troubleshoot these issues is essential for maintaining a secure network.
Common Troubleshooting Steps
Here are some common troubleshooting steps for IoT device monitoring:
- Check Device Connectivity: Ensure all devices are properly connected to the network.
- Review Configuration Settings: Verify that monitoring tools are correctly configured.
- Update Firmware: Ensure all devices have the latest firmware updates installed.
By addressing these issues promptly, you can minimize downtime and maintain the security of your network.
Best Practices for Monitoring IoT Devices
Adopting best practices for monitoring IoT devices is essential for ensuring the long-term security of your network. These practices encompass a range of strategies designed to enhance both security and efficiency.
Key Best Practices
Here are some key best practices for monitoring IoT devices:
- Regular Audits: Conduct regular audits of your network to identify potential vulnerabilities.
- Employee Training: Train employees on best practices for IoT device management and security.
- Third-Party Assessments: Consider hiring third-party security experts to assess your network's security.
Implementing these best practices ensures that your IoT ecosystem remains secure and efficient in the long term.
Conclusion
In conclusion, monitoring IoT devices behind a router is a critical practice for maintaining the security and integrity of your network. By understanding the risks associated with unmonitored devices, utilizing the right tools, and implementing best practices, you can create a secure environment for your IoT ecosystem.
We encourage you to take action by implementing the strategies discussed in this guide. Share your thoughts and experiences in the comments below, and don't hesitate to explore other articles on our site for more insights into network security.