Mastering RemoteIoT VPC SSH Download: A Comprehensive Guide
RemoteIoT VPC SSH download is a critical process for those who manage virtual private clouds (VPCs) and need secure access to their infrastructure. Whether you're a beginner or an experienced IT professional, understanding how to download and configure SSH keys for your RemoteIoT VPC is essential. This guide will walk you through everything you need to know, ensuring your data remains secure while optimizing your cloud management workflow.
With the rapid adoption of cloud computing, the ability to connect securely to your VPC has become a fundamental requirement for businesses and individuals alike. RemoteIoT VPC SSH download offers a robust solution to establish encrypted connections, ensuring that sensitive data is protected from unauthorized access.
As we delve deeper into this topic, you'll discover step-by-step instructions, expert tips, and best practices to enhance your knowledge of RemoteIoT VPC SSH download. By the end of this article, you'll be equipped with the skills to confidently manage your VPC environments and troubleshoot common issues that may arise during the setup process.
Introduction to RemoteIoT VPC
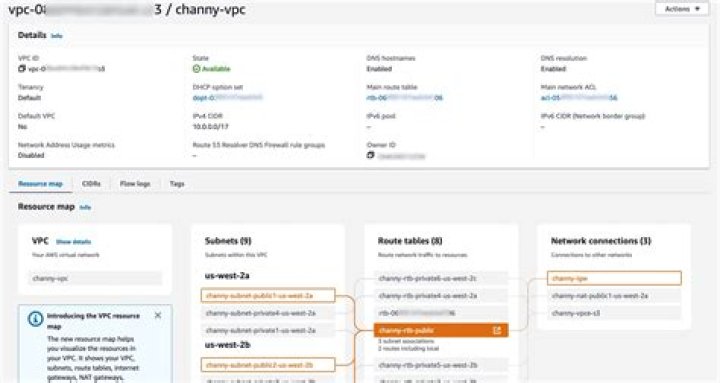
RemoteIoT VPC, or Virtual Private Cloud, is a cloud-based infrastructure solution designed to provide secure and isolated environments for deploying applications and services. It allows organizations to create a dedicated network space within the cloud, ensuring that resources are protected from external threats and unauthorized access.
Key Features of RemoteIoT VPC
- Private networking capabilities
- Customizable IP ranges
- Integration with other cloud services
- Scalability and flexibility
Understanding the basics of RemoteIoT VPC is crucial for anyone looking to implement secure cloud solutions. By leveraging its features, you can enhance the security and performance of your applications while maintaining control over your infrastructure.
What is SSH?
SSH, or Secure Shell, is a cryptographic network protocol used for secure communication over unsecured networks. It provides a secure way to access remote servers, transfer files, and execute commands, making it an essential tool for managing cloud environments like RemoteIoT VPC.
Benefits of Using SSH
- Encryption of data during transmission
- Authentication mechanisms to verify user identity
- Support for secure file transfers
SSH ensures that your interactions with RemoteIoT VPC remain secure and private, protecting sensitive information from potential threats.
RemoteIoT VPC SSH Download Process
Downloading SSH keys for your RemoteIoT VPC involves a series of steps that ensure secure access to your virtual private cloud. Below is a detailed breakdown of the process:
Step-by-Step Guide
- Log in to your RemoteIoT VPC management console
- Navigate to the SSH key management section
- Create a new SSH key pair or upload an existing one
- Download the private key file securely
- Save the key file in a secure location
By following these steps, you can ensure that your SSH keys are properly configured and ready for use in connecting to your RemoteIoT VPC.
Configuring SSH Keys
Once you've downloaded your SSH keys, the next step is configuring them to work with your RemoteIoT VPC environment. This involves setting up permissions, specifying key locations, and testing the connection.
Best Practices for SSH Key Configuration
- Use strong, unique passphrases for added security
- Store private keys in secure, restricted directories
- Limit access to SSH keys to authorized personnel only
Proper configuration of SSH keys is vital for maintaining the integrity and security of your RemoteIoT VPC setup.
Best Practices for SSH
Adopting best practices for SSH usage can significantly enhance the security and reliability of your RemoteIoT VPC environment. Here are some key recommendations:
Security Measures
- Disable password-based authentication in favor of key-based authentication
- Regularly rotate SSH keys to minimize exposure risks
- Monitor and audit SSH access logs for suspicious activity
Implementing these practices will help protect your RemoteIoT VPC from potential security breaches and unauthorized access.
Troubleshooting Common Issues
Despite careful setup and configuration, issues may arise when working with RemoteIoT VPC SSH. Here are some common problems and their solutions:
Common Problems and Fixes
- Connection Refused: Ensure that the SSH service is running and that firewall rules allow SSH traffic.
- Permission Denied: Verify that the correct SSH key is being used and that file permissions are set correctly.
- Timeout Errors: Check network connectivity and ensure that the server is reachable.
By addressing these issues promptly, you can maintain uninterrupted access to your RemoteIoT VPC environment.
Security Considerations
When managing RemoteIoT VPC SSH, security should always be a top priority. Here are some important considerations to keep in mind:
Enhancing Security
- Implement multi-factor authentication (MFA) for added protection
- Regularly update SSH software to patch vulnerabilities
- Limit SSH access to trusted IP addresses
By prioritizing security, you can safeguard your RemoteIoT VPC from potential threats and ensure the confidentiality of your data.
Use Cases of RemoteIoT VPC SSH
RemoteIoT VPC SSH has numerous applications across various industries. Below are some common use cases:
Industry Applications
- DevOps teams using SSH to deploy and manage applications
- IT administrators securing remote access to cloud resources
- Security professionals conducting penetration tests
These use cases demonstrate the versatility and importance of RemoteIoT VPC SSH in modern cloud environments.
Future Trends in RemoteIoT VPC
As technology continues to evolve, so do the capabilities of RemoteIoT VPC SSH. Here are some emerging trends to watch:
Technological Advancements
- Integration with AI-driven security solutions
- Increased adoption of quantum-resistant encryption
- Enhanced automation for SSH key management
Staying informed about these trends will help you leverage the full potential of RemoteIoT VPC SSH in the future.
Conclusion and Next Steps
In conclusion, mastering RemoteIoT VPC SSH download and configuration is essential for anyone working with cloud environments. By following the guidelines and best practices outlined in this article, you can ensure secure and efficient management of your VPC resources.
We encourage you to take the following actions:
- Experiment with the techniques discussed in this guide
- Share your insights and experiences in the comments section
- Explore additional resources on our website for further learning
Thank you for reading, and we hope this article has provided valuable insights into RemoteIoT VPC SSH download and management. Stay tuned for more informative content in the future!


