Mastering RemoteIoT Platform SSH Key for Raspberry Pi: A Comprehensive Guide

RemoteIoT platform SSH key configuration for Raspberry Pi is an essential skill for anyone working in the field of IoT and remote device management. Whether you're a beginner or an experienced professional, understanding how to set up and secure your Raspberry Pi using SSH keys can significantly enhance your device's security and functionality. This guide will walk you through everything you need to know, from the basics to advanced techniques, ensuring you can confidently manage your IoT devices remotely.
As the Internet of Things (IoT) continues to grow, the demand for secure and efficient remote access solutions has never been higher. One of the most popular platforms for IoT projects is the Raspberry Pi, a versatile single-board computer that can be configured for a wide range of applications. However, ensuring secure access to these devices is critical to protecting sensitive data and maintaining system integrity.
In this article, we will explore the RemoteIoT platform SSH key setup for Raspberry Pi in detail, covering everything from the basics of SSH keys to advanced security configurations. By the end of this guide, you'll have the knowledge and tools to implement secure remote access for your IoT projects.
Introduction to RemoteIoT Platform SSH Key
The RemoteIoT platform SSH key setup is a critical component of managing IoT devices securely. Secure Shell (SSH) is a cryptographic network protocol that allows users to access remote devices over an encrypted connection. By using SSH keys instead of passwords, you can enhance the security of your Raspberry Pi and reduce the risk of unauthorized access.
SSH keys provide a more secure alternative to traditional password authentication. They consist of two parts: a private key, which is kept secret on your local machine, and a public key, which is added to the remote device. When configured correctly, this system eliminates the need for passwords and reduces the likelihood of brute-force attacks.
Why Use SSH Keys for Raspberry Pi?
- Enhanced security: SSH keys are much harder to crack than passwords.
- Convenience: Once set up, you won't need to enter a password every time you connect.
- Automation: SSH keys enable seamless automation of tasks across multiple devices.
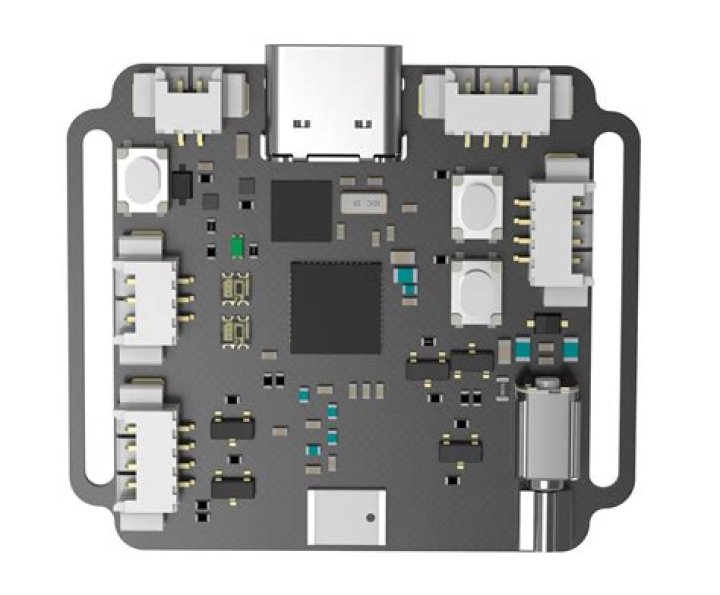
Raspberry Pi Overview
The Raspberry Pi is a low-cost, credit-card-sized computer that has become a staple in the world of IoT and embedded systems. It offers a range of features that make it ideal for both hobbyists and professionals, including:
- GPIO pins for interfacing with sensors and actuators.
- Support for various operating systems, including Raspbian and Ubuntu.
- Compatibility with a wide range of software and libraries.
When combined with the RemoteIoT platform, the Raspberry Pi becomes a powerful tool for managing IoT devices remotely. By configuring SSH keys, you can ensure that your device remains secure while still being accessible from anywhere in the world.
Understanding SSH Basics
Secure Shell (SSH) is a protocol that provides secure communication between two networked devices. It is widely used for remote command-line login and execution, file transfer, and tunneling. SSH uses encryption to protect data in transit, making it a secure alternative to unencrypted protocols like Telnet.
SSH operates on a client-server model, where the client initiates the connection and the server responds. The connection is established using public-key cryptography, which ensures that only authorized users can access the server.
How Does SSH Work?
When you connect to a remote device using SSH, the following steps occur:
- The client sends a connection request to the server.
- The server responds with its public key.
- The client verifies the server's identity using the public key.
- The client and server exchange keys to establish an encrypted session.
Generating SSH Keys
Generating SSH keys is a straightforward process that involves creating a public-private key pair. This pair will be used to authenticate your connection to the Raspberry Pi. Follow these steps to generate SSH keys on your local machine:
- Open a terminal or command prompt.
- Run the command
ssh-keygen -t rsa -b 4096to generate a 4096-bit RSA key. - Follow the prompts to specify a file location and passphrase (optional).
Once the keys are generated, you will have two files: id_rsa (private key) and id_rsa.pub (public key). The public key will be added to your Raspberry Pi, while the private key must be kept secure on your local machine.
Adding the Public Key to Raspberry Pi
To add the public key to your Raspberry Pi, follow these steps:
- Copy the public key to the Raspberry Pi using the command
ssh-copy-id user@raspberrypi. - Verify that the key has been added by checking the
~/.ssh/authorized_keysfile on the Raspberry Pi. - Test the connection by running
ssh user@raspberrypi. You should now be able to log in without entering a password.
Configuring RemoteIoT Platform
The RemoteIoT platform is designed to simplify the management of IoT devices. By integrating SSH key authentication, you can ensure that your devices remain secure while still being accessible from anywhere. Here's how to configure the RemoteIoT platform for SSH key access:
- Log in to the RemoteIoT platform using your credentials.
- Navigate to the device management section and select your Raspberry Pi.
- Upload your public SSH key to the platform's settings.
Benefits of Using RemoteIoT Platform
- Centralized device management.
- Real-time monitoring and alerts.
- Seamless integration with other IoT platforms.
Security Best Practices for SSH
While SSH keys provide a high level of security, there are additional steps you can take to further protect your Raspberry Pi:
- Disable password authentication in the SSH configuration file (
/etc/ssh/sshd_config). - Use a non-standard port for SSH to reduce the likelihood of automated attacks.
- Regularly update your operating system and software to patch known vulnerabilities.
By following these best practices, you can ensure that your Raspberry Pi remains secure even in the face of evolving threats.
Troubleshooting Common Issues
Even with careful setup, issues can arise when configuring SSH keys for Raspberry Pi. Here are some common problems and their solutions:
- Connection refused: Ensure that the SSH service is running on the Raspberry Pi and that the firewall allows incoming connections on port 22.
- Permission denied: Verify that the public key has been added to the
~/.ssh/authorized_keysfile and that the file permissions are set correctly. - Key not recognized: Check that the private key matches the public key and that the passphrase (if used) is correct.
Case Studies: Real-World Applications
To better understand the practical applications of RemoteIoT platform SSH key setup for Raspberry Pi, let's look at some real-world examples:
- Smart Home Automation: A homeowner uses Raspberry Pi with SSH keys to manage their smart home devices remotely, ensuring secure access from anywhere.
- Industrial IoT: A manufacturing company deploys Raspberry Pi devices with SSH key authentication to monitor production lines and collect data securely.
Comparison with Other Platforms
While the RemoteIoT platform offers many advantages for managing IoT devices, it's worth comparing it to other platforms:
- Amazon Web Services (AWS) IoT: Offers robust scalability and integration with other AWS services.
- Microsoft Azure IoT Hub: Provides advanced analytics and machine learning capabilities.
Ultimately, the choice of platform depends on your specific needs and requirements. The RemoteIoT platform is an excellent option for those looking for a user-friendly and secure solution for managing IoT devices.
Conclusion and Next Steps
In conclusion, mastering RemoteIoT platform SSH key setup for Raspberry Pi is an essential skill for anyone working in the field of IoT. By following the steps outlined in this guide, you can ensure that your devices remain secure while still being accessible from anywhere in the world.
Take action today by implementing SSH key authentication for your Raspberry Pi. Leave a comment below sharing your experience or questions, and don't forget to explore other articles on our site for more IoT tips and tricks.