Mastering RemoteIoT Device SSH: A Comprehensive Guide
In today's interconnected world, remoteIoT device SSH has become an essential tool for managing and securing Internet of Things (IoT) devices remotely. Whether you're a tech enthusiast, a network administrator, or a security professional, understanding how to leverage SSH for remote IoT management is crucial. This article will provide you with an in-depth exploration of remoteIoT device SSH, covering everything from the basics to advanced techniques.
IoT devices are revolutionizing industries, but their widespread adoption comes with unique challenges, particularly in terms of security and management. Remote SSH offers a secure way to access and control these devices from anywhere in the world. This guide will help you navigate the complexities of remoteIoT device SSH and equip you with the knowledge to enhance your IoT infrastructure.
By the end of this article, you will have a comprehensive understanding of how remoteIoT device SSH works, its benefits, potential risks, and best practices for implementation. Let's dive in!
Introduction to RemoteIoT Device SSH
RemoteIoT device SSH is a powerful technology that allows users to securely access and manage IoT devices from remote locations. This capability is particularly valuable in industries such as manufacturing, agriculture, healthcare, and smart cities, where IoT devices are deployed across vast geographical areas. By leveraging SSH, organizations can ensure that their IoT infrastructure remains secure and operational at all times.
Understanding IoT and Its Challenges
The Internet of Things (IoT) refers to the network of physical devices embedded with sensors, software, and connectivity capabilities. While IoT offers numerous benefits, it also introduces challenges related to security, scalability, and management. RemoteIoT device SSH addresses these challenges by providing a secure and reliable method for accessing IoT devices remotely.
Key Features of RemoteIoT Device SSH
- Encrypted communication
- Authentication mechanisms
- Command execution capabilities
- File transfer functionality
What is SSH?
SSH, or Secure Shell, is a cryptographic network protocol designed for secure communication over unsecured networks. It provides a secure channel for data exchange between two parties, ensuring confidentiality, integrity, and authentication. SSH is widely used in IT environments for remote server management, file transfers, and automation tasks.
SSH vs. Telnet
While both SSH and Telnet allow remote access to devices, SSH offers superior security features. Unlike Telnet, which transmits data in plaintext, SSH encrypts all communication, making it resistant to eavesdropping and tampering.
Why RemoteIoT Device SSH is Important
As IoT devices continue to proliferate, the need for secure and efficient management solutions becomes increasingly critical. RemoteIoT device SSH plays a vital role in addressing this need by enabling administrators to:
- Monitor device performance in real-time
- Perform updates and configurations remotely
- Diagnose and resolve issues without physical access
- Enhance overall security posture
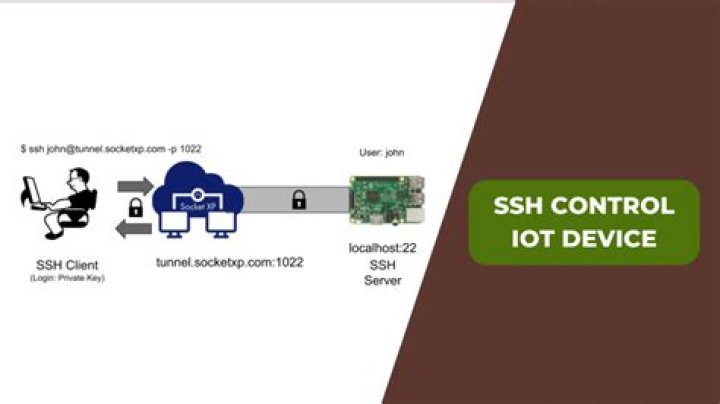
How RemoteIoT Device SSH Works
RemoteIoT device SSH operates by establishing a secure connection between a client and a server. The process involves several key steps:
- Authentication: The client verifies its identity using credentials such as passwords or public key pairs.
- Encryption: All data exchanged between the client and server is encrypted using advanced cryptographic algorithms.
- Command Execution: Once authenticated, the client can execute commands on the server or IoT device.
Key Components of SSH
- SSH Client: The software used to initiate the connection.
- SSH Server: The software running on the IoT device that listens for incoming connections.
- SSH Keys: Cryptographic keys used for authentication and encryption.
Benefits of Using RemoteIoT Device SSH
Implementing remoteIoT device SSH offers numerous advantages, including:
- Enhanced Security: SSH encrypts all communication, protecting sensitive data from unauthorized access.
- Improved Efficiency: Administrators can manage multiple devices simultaneously without the need for physical presence.
- Cost Savings: Remote management reduces the need for on-site technicians, resulting in significant cost savings.
- Scalability: SSH can handle large numbers of devices, making it suitable for enterprise-level deployments.
Common SSH Commands for RemoteIoT Devices
Mastering SSH commands is essential for effective remoteIoT device management. Some commonly used commands include:
ssh user@hostname: Establishes a connection to the remote device.scp file user@hostname:/path: Transfers files between the local and remote systems.ssh-keygen: Generates public and private key pairs for authentication.
Security Considerations for RemoteIoT Device SSH
While SSH is a secure protocol, it is not immune to attacks. To mitigate potential risks, organizations should:
- Use strong passwords and public key authentication.
- Disable root login to prevent unauthorized access.
- Regularly update SSH software to address vulnerabilities.
- Implement firewalls and intrusion detection systems.
SSH Vulnerabilities
Common vulnerabilities associated with SSH include brute-force attacks, man-in-the-middle attacks, and misconfigured servers. Staying informed about the latest security trends and best practices is crucial for maintaining a robust defense.
Troubleshooting RemoteIoT Device SSH
Despite its reliability, SSH connections can occasionally fail. Common issues and their solutions include:
- Connection Refused: Ensure that the SSH service is running on the remote device and that the firewall allows incoming connections.
- Authentication Failure: Verify that the correct credentials or keys are being used.
- Timeout Errors: Check network connectivity and adjust the SSH timeout settings if necessary.
Best Practices for RemoteIoT Device SSH
To maximize the effectiveness of remoteIoT device SSH, organizations should adhere to the following best practices:
- Implement role-based access control to limit user privileges.
- Monitor SSH logs for suspicious activities.
- Use SSH tunnels for secure data transmission.
- Regularly audit SSH configurations and settings.
Future Trends in RemoteIoT Device SSH
As technology continues to evolve, remoteIoT device SSH is likely to incorporate advancements such as:
- Quantum-resistant encryption algorithms.
- Integration with AI and machine learning for automated threat detection.
- Enhanced usability through graphical user interfaces.
Conclusion
RemoteIoT device SSH is a critical tool for managing and securing IoT devices in today's connected world. By understanding its principles, benefits, and best practices, organizations can harness its full potential to enhance their IoT infrastructure. We encourage you to explore the topics covered in this article further and apply them to your own projects.
Feel free to leave a comment below if you have any questions or suggestions. Don't forget to share this article with others who may find it valuable. For more insightful content, explore our other articles on IoT and cybersecurity.