Mastering Remote IoT VPC SSH: A Comprehensive Guide to Secure Downloads and Connections
In today's digital age, remote IoT VPC SSH download capabilities have become increasingly essential for managing and securing connected devices. As businesses expand their digital footprint, ensuring secure access to virtual private cloud (VPC) environments through SSH protocols is crucial for maintaining data integrity and operational efficiency.
Remote IoT management has revolutionized the way organizations handle their devices and networks. By leveraging secure protocols like SSH, businesses can remotely access IoT devices within a VPC, enabling them to monitor performance, update firmware, and troubleshoot issues without physical presence. This level of accessibility not only enhances operational flexibility but also improves overall security.
This article delves into the intricacies of remote IoT VPC SSH download processes, offering practical insights and expert advice to help you navigate the complexities of secure remote access. Whether you're a seasoned IT professional or a newcomer to the world of IoT, this guide will provide you with the knowledge and tools necessary to implement robust security measures for your VPC environments.
Introduction to Remote IoT VPC SSH
What is Remote IoT VPC SSH?
Remote IoT VPC SSH refers to the practice of securely accessing Internet of Things (IoT) devices located within a Virtual Private Cloud (VPC) using the Secure Shell (SSH) protocol. This method allows users to manage and interact with IoT devices remotely, ensuring both convenience and security. The SSH protocol encrypts all data transmitted between the user's device and the IoT device, making it an ideal choice for safeguarding sensitive information.
As the number of IoT devices continues to grow, the need for secure remote access becomes increasingly important. Organizations must implement robust security measures to protect their networks and devices from unauthorized access and potential cyber threats. Remote IoT VPC SSH provides a reliable solution for managing IoT devices while maintaining the highest level of security.
Benefits of Using Remote IoT VPC SSH
- Enhanced security through encrypted connections
- Improved operational efficiency with remote access capabilities
- Cost-effective solution for managing large-scale IoT deployments
- Flexibility to monitor and manage devices from anywhere in the world
The Importance of Secure Connections
In today's interconnected world, securing your IoT devices is paramount. With the increasing number of cyberattacks targeting IoT networks, ensuring secure connections has become a top priority for organizations. Remote IoT VPC SSH offers a secure method for accessing and managing IoT devices, protecting sensitive data and maintaining network integrity.
Secure connections are vital for protecting against unauthorized access, data breaches, and other cyber threats. By implementing robust security measures, organizations can safeguard their networks and devices, ensuring the smooth operation of their IoT ecosystems. Remote IoT VPC SSH plays a crucial role in this process, providing a secure and reliable method for managing IoT devices.
Understanding VPC and SSH
What is a Virtual Private Cloud (VPC)?
A Virtual Private Cloud (VPC) is a secure and isolated network environment within a cloud platform. It allows organizations to host their resources, such as IoT devices and applications, in a private and secure setting. VPCs provide enhanced security and control over network traffic, ensuring that only authorized users can access the resources within the VPC.
What is Secure Shell (SSH)?
Secure Shell (SSH) is a cryptographic network protocol used for secure communication over an unsecured network. It provides a secure channel for accessing remote devices and transferring data, ensuring the confidentiality and integrity of the information being transmitted. SSH is widely used in IoT environments for managing devices and securing network connections.
Setting Up Remote IoT VPC SSH
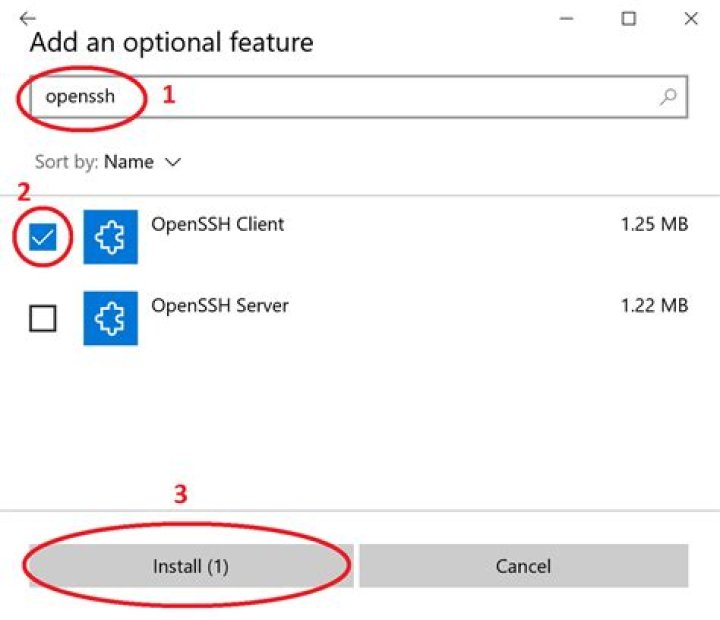
Step-by-Step Guide to Configuring SSH in VPC
Setting up remote IoT VPC SSH involves several steps, including configuring the VPC, enabling SSH access, and securing the connection. Follow the steps below to successfully set up SSH for your IoT devices:
- Create a VPC and configure its settings to meet your organization's requirements.
- Enable SSH access for the IoT devices within the VPC.
- Generate SSH keys and distribute them to authorized users.
- Configure firewall rules to allow SSH traffic while blocking unauthorized access.
- Test the connection to ensure secure access to your IoT devices.
Best Practices for SSH Configuration
- Use strong, unique passwords for SSH access.
- Implement two-factor authentication for added security.
- Regularly update SSH software to address security vulnerabilities.
- Monitor SSH logs for suspicious activity and potential security threats.
Enhancing Security Measures
Securing Your IoT Devices with SSH
While SSH provides a secure method for accessing IoT devices, additional security measures can further enhance the protection of your VPC environment. Implementing firewalls, intrusion detection systems, and regular security audits can help safeguard your IoT devices and network from potential threats.
Common Security Threats in IoT Networks
- Unauthorized access to IoT devices
- Data breaches and information theft
- Distributed Denial of Service (DDoS) attacks
- Malware infections and ransomware attacks
Troubleshooting Common Issues
Identifying and Resolving SSH Connection Problems
Despite its robust security features, SSH connections can sometimes encounter issues. Common problems include incorrect SSH keys, firewall restrictions, and network connectivity issues. To resolve these problems, follow the troubleshooting steps below:
- Verify that the correct SSH keys are being used.
- Check firewall rules to ensure SSH traffic is allowed.
- Test network connectivity to confirm proper access to the VPC.
- Consult SSH logs for additional information on connection issues.
Essential Tools for Remote IoT Management
Software and Applications for Managing IoT Devices
Several tools and applications are available to help manage IoT devices within a VPC environment. These tools offer features such as device monitoring, firmware updates, and remote access capabilities, enhancing the overall efficiency of IoT management. Some popular tools include:
- Amazon IoT Core
- Microsoft Azure IoT Hub
- Google Cloud IoT Core
- IBM Watson IoT Platform
Best Practices for Secure Downloads
Ensuring Secure Data Transfer with SSH
When downloading data from IoT devices within a VPC, it's essential to follow best practices to ensure secure data transfer. These practices include using encrypted connections, verifying data integrity, and implementing access controls. By adhering to these guidelines, you can protect your data and maintain the security of your IoT network.
Key Considerations for Secure Downloads
- Use SSH for all data transfer activities.
- Verify the integrity of downloaded files using checksums.
- Implement role-based access controls to restrict data access.
- Regularly audit download activities to detect potential security breaches.
Future Trends in Remote IoT VPC SSH
As technology continues to evolve, new trends and innovations are emerging in the field of remote IoT VPC SSH. These advancements aim to enhance security, improve efficiency, and expand the capabilities of IoT management. Some notable trends include:
- Increased adoption of quantum-resistant encryption for SSH connections.
- Integration of artificial intelligence and machine learning for predictive maintenance and threat detection.
- Expansion of edge computing for faster data processing and reduced latency.
- Development of new protocols and standards for securing IoT communications.
Conclusion
Remote IoT VPC SSH offers a secure and reliable method for managing IoT devices within a virtual private cloud environment. By implementing robust security measures and following best practices, organizations can protect their networks and devices from potential threats while enhancing operational efficiency. As technology continues to evolve, staying informed about emerging trends and innovations in remote IoT VPC SSH will be crucial for maintaining a secure and effective IoT ecosystem.
We encourage you to share your thoughts and experiences with remote IoT VPC SSH in the comments section below. Additionally, feel free to explore other articles on our site for more insights into IoT security and management. Together, we can build a safer and more connected world.