Mastering IoT SSH Connection to AWS: A Comprehensive Guide
In the rapidly evolving world of technology, the Internet of Things (IoT) has become a cornerstone for innovation, especially when integrated with cloud platforms like AWS. IoT SSH connect AWS is a critical process that enables secure communication between IoT devices and the cloud. Understanding this integration is essential for anyone looking to build scalable and secure IoT solutions.
As more businesses and developers embrace IoT, the need for secure and efficient connectivity has never been more important. IoT devices generate vast amounts of data that require robust infrastructure to process and analyze. AWS provides the perfect ecosystem for managing IoT data securely, and SSH plays a pivotal role in ensuring encrypted communication.
This guide aims to provide a detailed exploration of IoT SSH connect AWS, offering insights into the technical aspects, best practices, and practical applications. Whether you're a beginner or an experienced developer, this article will equip you with the knowledge needed to leverage this powerful technology.
Introduction to IoT
The Internet of Things (IoT) refers to the network of physical objects embedded with sensors, software, and connectivity, enabling them to exchange data with other devices and systems over the internet. IoT has transformed industries by enabling smart homes, wearable devices, industrial automation, and more. According to Gartner, the number of IoT devices is projected to surpass 25 billion by 2025.
IoT devices generate massive amounts of data that require secure and efficient processing. This is where cloud platforms like AWS come into play, offering scalable infrastructure to manage IoT data seamlessly.
Connecting IoT devices to AWS using SSH ensures secure communication, protecting sensitive data from unauthorized access. This integration is crucial for maintaining the integrity of IoT ecosystems.
Understanding AWS
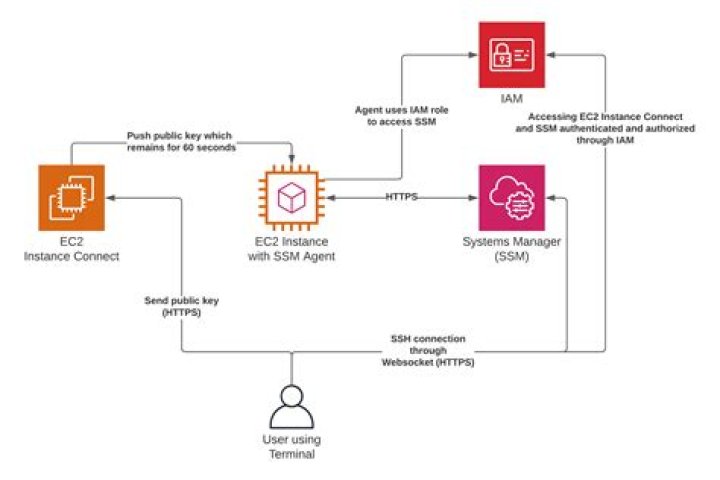
Amazon Web Services (AWS) is a comprehensive cloud platform that provides a wide range of services, including compute power, storage, databases, and more. AWS IoT Core is specifically designed to facilitate communication between IoT devices and the cloud. It supports MQTT, HTTP, and WebSocket protocols, making it versatile for various use cases.
AWS also offers robust security features, including IAM roles, VPCs, and encryption, ensuring that IoT data is protected at every stage. By leveraging AWS services, developers can build secure and scalable IoT solutions that meet the demands of modern applications.
Connecting IoT devices to AWS using SSH enhances security by encrypting data during transmission, providing an additional layer of protection against cyber threats.
Overview of SSH
Secure Shell (SSH) is a cryptographic network protocol used for secure communication over unsecured networks. It provides strong authentication and encrypted data communications, making it an ideal choice for securing IoT connections. SSH is widely used in IT infrastructure for remote server management, file transfers, and tunneling.
When integrating IoT devices with AWS, SSH ensures that data transmitted between devices and the cloud is encrypted and secure. This is particularly important for applications that handle sensitive information, such as healthcare or financial systems.
SSH uses public-key cryptography to authenticate devices and encrypt data, reducing the risk of unauthorized access. By leveraging SSH, developers can build secure IoT solutions that comply with industry standards and regulations.
IoT SSH Connect AWS
Connecting IoT devices to AWS using SSH involves setting up a secure communication channel between the device and the cloud. This process ensures that data transmitted between the two is encrypted and protected from interception. IoT SSH connect AWS is a critical component of secure IoT ecosystems, enabling developers to build robust and scalable applications.
To establish an IoT SSH connection to AWS, developers need to configure the necessary security settings, including SSH keys, firewalls, and network configurations. This ensures that only authorized devices can access the cloud infrastructure, minimizing the risk of unauthorized access.
By integrating SSH with AWS IoT Core, developers can leverage the power of the cloud to manage IoT data securely and efficiently. This integration supports various use cases, from smart home automation to industrial IoT applications.
Setup Process
Prerequisites
Before setting up an IoT SSH connection to AWS, ensure you have the following prerequisites in place:
- An AWS account with appropriate permissions.
- An IoT device with SSH capabilities.
- A valid SSH key pair for authentication.
- A configured VPC and security group to control access.
These prerequisites are essential for establishing a secure and reliable connection between IoT devices and AWS.
Installation Steps
Follow these steps to set up an IoT SSH connection to AWS:
- Install the necessary software on your IoT device, including an SSH client and AWS SDK.
- Create an SSH key pair in AWS and download the private key securely.
- Configure the security group to allow SSH traffic from your IoT device's IP address.
- Establish an SSH connection from the IoT device to the AWS instance using the private key.
- Test the connection by transferring data between the device and the cloud.
These steps ensure a secure and efficient connection, enabling seamless communication between IoT devices and AWS.
Security Best Practices
When integrating IoT devices with AWS using SSH, it's crucial to follow best practices to ensure maximum security. Below are some recommendations:
- Use strong SSH keys: Generate long, complex SSH keys to enhance security.
- Disable password authentication: Use public-key authentication instead of passwords to reduce the risk of brute-force attacks.
- Limit SSH access: Restrict SSH access to specific IP addresses or ranges to minimize exposure.
- Regularly update software: Keep your IoT devices and AWS instances up to date with the latest security patches.
- Monitor logs: Regularly review SSH logs to detect and respond to suspicious activities.
By adhering to these best practices, developers can build secure IoT solutions that protect sensitive data and maintain the integrity of their systems.
Troubleshooting Common Issues
While setting up an IoT SSH connection to AWS, you may encounter various issues. Below are some common problems and their solutions:
- Connection refused: Ensure that the security group allows SSH traffic and that the correct IP address is specified.
- Authentication failure: Verify that the SSH key pair is correctly configured and that the private key is accessible.
- Timeout errors: Check network configurations and ensure that there are no firewalls blocking the connection.
- Data transfer issues: Test the connection using simple commands and ensure that the necessary software is installed on both ends.
By addressing these issues promptly, developers can ensure a smooth and secure connection between IoT devices and AWS.
Use Cases
The integration of IoT SSH connect AWS has numerous applications across various industries. Below are some examples:
- Smart Home Automation: Securely manage smart home devices and monitor their performance in real time.
- Industrial IoT: Monitor and control industrial equipment remotely, ensuring optimal performance and reducing downtime.
- Healthcare: Securely transmit patient data from IoT devices to cloud-based systems for analysis and diagnosis.
- Retail: Optimize inventory management and enhance customer experience through IoT-enabled systems.
These use cases demonstrate the versatility and potential of IoT SSH connect AWS in transforming industries and driving innovation.
Performance Optimization
To optimize the performance of IoT SSH connect AWS, consider the following strategies:
- Use compression: Enable SSH compression to reduce data transfer times and improve efficiency.
- Optimize network configurations: Ensure that network settings are optimized for low latency and high throughput.
- Monitor resource usage: Regularly monitor CPU, memory, and disk usage to identify and address bottlenecks.
- Scale horizontally: Use AWS Auto Scaling to handle increased loads during peak usage periods.
By implementing these strategies, developers can enhance the performance of their IoT solutions, ensuring smooth and reliable operation.
Conclusion
In conclusion, IoT SSH connect AWS is a powerful tool for building secure and scalable IoT solutions. By leveraging SSH for encrypted communication, developers can protect sensitive data and maintain the integrity of their systems. This guide has provided a comprehensive overview of the technical aspects, best practices, and practical applications of IoT SSH connect AWS.
We encourage readers to experiment with the setup process and explore the various use cases discussed in this article. For further learning, consider exploring AWS documentation and community forums for additional insights and support. Don't forget to share your thoughts and experiences in the comments section below, and feel free to explore other articles on our site for more information on IoT and cloud technologies.