IoT SSH Over SSH Example: A Comprehensive Guide
IoT SSH over SSH example is a crucial topic for developers and engineers working in the realm of Internet of Things (IoT). This article will delve into the intricacies of using SSH within an IoT environment and provide practical examples to help you secure your IoT network.
In today's interconnected world, IoT devices are rapidly becoming an integral part of our daily lives. However, securing these devices is a significant challenge. One effective way to enhance security is through SSH tunneling, which allows encrypted communication between devices. Understanding IoT SSH over SSH examples can significantly improve the security of your IoT infrastructure.
This article will provide a detailed exploration of IoT SSH over SSH, including practical examples, security considerations, and best practices. Whether you're a beginner or an experienced professional, this guide will equip you with the knowledge needed to implement secure IoT solutions.
Introduction to IoT SSH Over SSH
IoT SSH over SSH example refers to the practice of establishing secure communication between IoT devices using SSH tunneling. SSH (Secure Shell) is a cryptographic network protocol that provides secure communication over an unsecured network. In the context of IoT, SSH can be used to create encrypted tunnels for data transmission, ensuring that sensitive information remains protected from unauthorized access.
As IoT devices become more prevalent, the need for robust security measures becomes increasingly important. SSH over SSH offers a reliable solution for securing IoT communications, making it an essential tool for developers and network administrators. This section will explore the basics of SSH and its application in IoT environments.
Understanding SSH Basics
Before diving into IoT SSH over SSH examples, it's essential to understand the fundamentals of SSH. SSH is a protocol that enables secure remote login and other secure network services over an insecure network. It uses encryption to protect data in transit and authentication mechanisms to ensure the identity of the communicating parties.
Key Features of SSH
- Encryption: SSH encrypts all data transmitted between devices, making it difficult for attackers to intercept sensitive information.
- Authentication: SSH supports various authentication methods, including password-based and public key authentication, ensuring only authorized users can access the system.
- Integrity: SSH ensures data integrity by using cryptographic hash functions to detect any tampering during transmission.
Understanding these features is crucial for implementing secure IoT solutions using SSH.
Overview of IoT
The Internet of Things (IoT) refers to the network of physical devices embedded with sensors, software, and connectivity, enabling them to collect and exchange data. IoT devices range from simple sensors to complex industrial machinery, all designed to enhance efficiency and automation in various industries.
However, the rapid growth of IoT also brings significant security challenges. Devices often lack robust security features, making them vulnerable to attacks. This is where SSH over SSH comes into play, providing a secure communication channel for IoT devices.
Why Use SSH in IoT?
SSH is a powerful tool for securing IoT communications due to its ability to provide encryption, authentication, and integrity. Using SSH in IoT environments offers several benefits:
- Enhanced Security: SSH encrypts all data transmitted between devices, reducing the risk of data breaches.
- Remote Access: SSH allows secure remote access to IoT devices, enabling administrators to manage and monitor systems from anywhere.
- Scalability: SSH can be easily scaled to accommodate large IoT networks, ensuring consistent security across all devices.
By leveraging SSH, IoT developers can build more secure and reliable systems.
SSH Over SSH Explained
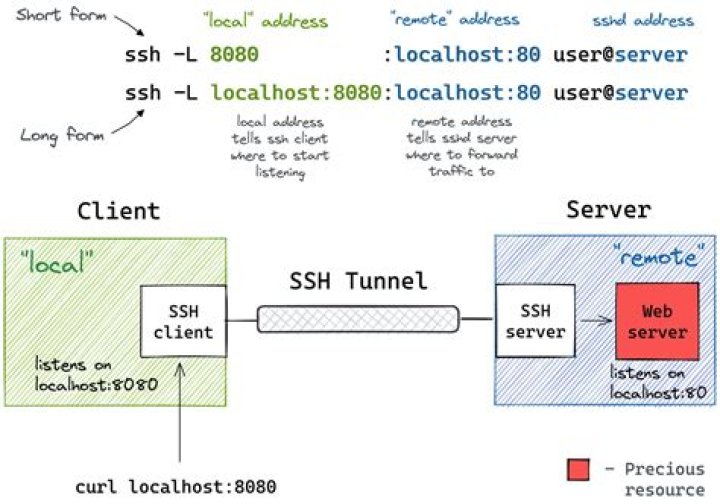
SSH over SSH involves creating a secure tunnel within another SSH connection. This technique is particularly useful in IoT environments where multiple layers of security are required. By encapsulating one SSH connection within another, data transmission becomes even more secure, protecting it from potential threats.
How SSH Over SSH Works
When implementing SSH over SSH, the inner SSH connection is encapsulated within the outer SSH connection. This creates a double layer of encryption, making it extremely difficult for attackers to intercept or tamper with the data. The process involves:
- Establishing the outer SSH connection.
- Creating the inner SSH connection within the outer tunnel.
- Transmitting data through the secure tunnel.
This method is especially beneficial for IoT devices operating in high-risk environments.
IoT SSH Over SSH Example
To better understand how SSH over SSH works in IoT, consider the following example:
Imagine a smart home system consisting of multiple IoT devices, such as smart thermostats, security cameras, and lighting systems. To ensure secure communication between these devices, SSH over SSH can be implemented. The process involves:
- Setting up an outer SSH connection between the central control unit and a remote server.
- Creating an inner SSH connection between individual IoT devices and the central control unit.
- Transmitting all data through the secure SSH tunnel, ensuring it remains protected from unauthorized access.
This example demonstrates how SSH over SSH can enhance the security of IoT networks.
Security Considerations
While SSH over SSH provides robust security, there are several considerations to keep in mind when implementing it in IoT environments:
- Key Management: Proper management of SSH keys is crucial to prevent unauthorized access. Ensure keys are stored securely and regularly updated.
- Network Configuration: Configure firewalls and network settings to restrict access to SSH ports, reducing the risk of unauthorized connections.
- Regular Updates: Keep all IoT devices and SSH software up to date with the latest security patches to protect against vulnerabilities.
By addressing these considerations, you can maximize the security benefits of SSH over SSH in IoT.
Best Practices for IoT SSH
To ensure the successful implementation of SSH in IoT environments, follow these best practices:
- Use Strong Passwords: Encourage the use of strong, complex passwords for SSH authentication to prevent brute-force attacks.
- Enable Public Key Authentication: Public key authentication offers a more secure alternative to password-based authentication, reducing the risk of unauthorized access.
- Monitor Activity: Regularly monitor SSH activity for any suspicious behavior, allowing you to quickly respond to potential security threats.
These practices will help you build a secure and reliable IoT infrastructure.
Tools and Resources
Several tools and resources are available to assist with implementing SSH in IoT environments:
- OpenSSH: A widely used SSH implementation that provides secure communication for IoT devices.
- SSHGuard: A tool that protects SSH servers from brute-force attacks by monitoring and blocking suspicious activity.
- Documentation: Refer to official SSH documentation and community forums for guidance on implementing SSH in IoT environments.
Utilizing these resources can streamline the process of securing your IoT network with SSH.
Future of IoT SSH
As IoT continues to evolve, the role of SSH in securing IoT communications will become increasingly important. Advances in encryption technology and the development of new protocols will further enhance the security of SSH, making it an even more powerful tool for protecting IoT devices.
In the future, we can expect to see more widespread adoption of SSH in IoT environments, driven by the growing need for secure communication in an increasingly interconnected world.
Conclusion
IoT SSH over SSH example provides a practical solution for securing IoT communications. By understanding the basics of SSH and its application in IoT environments, developers and network administrators can build more secure and reliable systems. Remember to follow best practices and utilize available tools and resources to maximize the security benefits of SSH in IoT.
We encourage you to leave a comment or share this article with others who may find it useful. For more information on IoT and SSH, explore our other articles and resources.