How to Use Remote IoT Behind Firewall on Mac: A Comprehensive Guide
In today's interconnected world, leveraging IoT devices remotely while maintaining security is crucial. Learning how to use remote IoT behind a firewall on Mac opens up new possibilities for managing smart devices securely. Whether you're a tech enthusiast or a professional, understanding this concept ensures your network remains both functional and protected.
As more organizations and individuals adopt IoT technology, the need for secure remote access becomes increasingly important. Firewalls are essential components of network security, but they can sometimes hinder access to IoT devices. This guide will provide a detailed explanation of how to navigate these challenges while ensuring seamless connectivity.
This article aims to equip readers with the knowledge and tools necessary to use remote IoT behind a firewall on Mac effectively. By following the steps outlined here, you'll gain the confidence to manage your IoT devices securely and efficiently, even when working remotely.
Introduction to IoT and Firewalls
The Internet of Things (IoT) has revolutionized how we interact with technology. From smart homes to industrial automation, IoT devices play a pivotal role in enhancing productivity and convenience. However, managing these devices remotely often requires navigating through firewalls, which are designed to protect networks from unauthorized access.
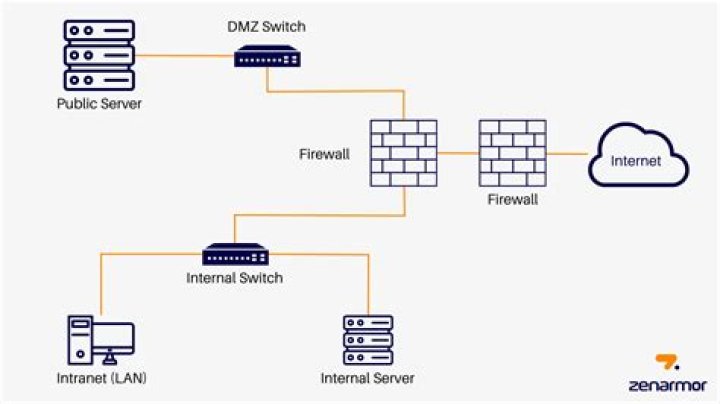
A firewall acts as a barrier between your internal network and external threats, filtering traffic based on predefined rules. While this is essential for security, it can sometimes block legitimate access to IoT devices. Understanding how to configure your firewall to allow secure remote access is crucial for maintaining functionality without compromising security.
What Is Remote IoT?
Remote IoT refers to the ability to control and monitor IoT devices from a distance. This capability is particularly valuable for businesses that rely on IoT for operations, allowing them to manage devices without being physically present. By learning how to use remote IoT behind a firewall on Mac, you can ensure uninterrupted access to your devices.
Why Remote Access Is Necessary
Remote access to IoT devices offers several advantages, including enhanced flexibility, improved efficiency, and reduced operational costs. Whether you're troubleshooting a device issue or performing routine maintenance, being able to access your IoT devices remotely saves time and resources.
For example, a business with multiple locations can centralize its IoT management, allowing IT teams to monitor and update devices across all sites from a single location. This centralized control streamlines operations and ensures consistency in device management.
Benefits of Remote IoT Access
- Increased operational efficiency
- Reduced downtime and maintenance costs
- Improved scalability and flexibility
- Enhanced data collection and analysis
Understanding Firewalls and Their Role
Firewalls are essential components of network security, designed to protect against unauthorized access and potential threats. They work by filtering incoming and outgoing traffic based on specific rules and policies. For remote IoT access, configuring your firewall correctly is critical to ensuring secure communication between your Mac and IoT devices.
Modern firewalls offer advanced features such as intrusion detection, traffic inspection, and encryption, making them powerful tools for securing your network. However, these features can sometimes block legitimate connections, requiring careful configuration to allow access to IoT devices.
Types of Firewalls
- Packet-filtering firewalls
- Stateful inspection firewalls
- Application-layer firewalls
- Next-generation firewalls
Secure Remote Access Methods
There are several methods for achieving secure remote access to IoT devices behind a firewall. These methods vary in complexity and security level, so it's important to choose the one that best suits your needs.
Popular Remote Access Protocols
- SSH (Secure Shell)
- VPN (Virtual Private Network)
- TLS/SSL (Transport Layer Security/Secure Sockets Layer)
Each of these protocols offers different levels of security and ease of implementation. For example, SSH is a popular choice for secure command-line access, while VPN provides a more comprehensive solution for accessing entire networks securely.
Steps to Configure Remote IoT Behind Firewall on Mac
Configuring remote IoT access behind a firewall on Mac involves several steps. Below is a detailed guide to help you set up secure connections:
Step 1: Identify Your IoT Devices
Begin by identifying the IoT devices you wish to access remotely. Make a note of their IP addresses, ports, and any specific requirements for remote access.
Step 2: Configure Your Firewall
Adjust your firewall settings to allow incoming and outgoing traffic for the specified IoT devices. This may involve creating custom rules or using predefined profiles provided by your firewall software.
Step 3: Set Up Secure Connections
Choose a secure protocol such as SSH or VPN to establish connections between your Mac and IoT devices. Follow the setup instructions for your chosen method, ensuring all security settings are properly configured.
Step 4: Test Your Connection
Once everything is set up, test your connection to ensure it works as expected. This may involve sending test commands or accessing device interfaces to verify functionality.
Troubleshooting Common Issues
Despite careful planning, issues can arise when configuring remote IoT access. Below are some common problems and their solutions:
Problem: Unable to Connect to IoT Device
Solution: Verify that your firewall rules are correctly configured and that the specified ports are open. Check your network settings to ensure there are no conflicts or misconfigurations.
Problem: Slow Connection Speed
Solution: Optimize your network settings and consider using a faster connection method if available. Ensure that your IoT devices are not overloaded with requests, which can slow down performance.
Best Practices for Secure IoT Management
Adopting best practices for IoT management ensures that your devices remain secure and functional. Below are some recommendations:
- Regularly update firmware and software to address security vulnerabilities
- Use strong, unique passwords for all IoT devices
- Limit access to authorized personnel only
- Monitor network activity for suspicious behavior
Tools and Software Recommendations
Several tools and software solutions are available to assist with remote IoT management. Some popular options include:
- WireGuard for secure VPN connections
- SSH clients such as PuTTY or Terminal
- Network monitoring tools like Wireshark
Security Considerations and Tips
Security should always be a top priority when managing IoT devices remotely. Below are some tips to enhance security:
- Implement multi-factor authentication for added protection
- Encrypt all data transmissions to prevent interception
- Regularly audit your network for potential vulnerabilities
Conclusion and Next Steps
Learning how to use remote IoT behind a firewall on Mac is an essential skill for anyone working with IoT technology. By following the steps outlined in this guide, you can ensure secure and efficient access to your devices, even from remote locations.
We encourage you to share your thoughts and experiences in the comments below. Additionally, explore our other articles for more insights into IoT technology and network security. Together, we can build a safer and more connected future.
Remember, the key to successful IoT management lies in balancing functionality with security. Stay informed, stay vigilant, and keep your network protected.


