How to Securely Connect Remote IoT VPC with Raspberry Pi for Seamless Download

Connecting IoT devices remotely through a Virtual Private Cloud (VPC) using Raspberry Pi has become a necessity in today's interconnected world. Businesses and individuals alike are leveraging the power of IoT to automate processes, monitor data in real-time, and enhance productivity. However, ensuring secure communication is critical to protect sensitive information from unauthorized access.
In this article, we will explore the methods and best practices to securely connect remote IoT VPC with Raspberry Pi for reliable data transmission. As IoT devices continue to grow in number, the importance of secure connections cannot be overstated. Without proper security measures, these devices become vulnerable to cyber threats, potentially leading to data breaches and operational disruptions.
This guide will provide you with step-by-step instructions, practical tips, and expert advice to help you set up a secure connection for your IoT VPC using Raspberry Pi. Whether you're a beginner or an experienced professional, this article aims to equip you with the knowledge and tools needed to safeguard your IoT infrastructure.
Introduction to IoT VPC and Raspberry Pi
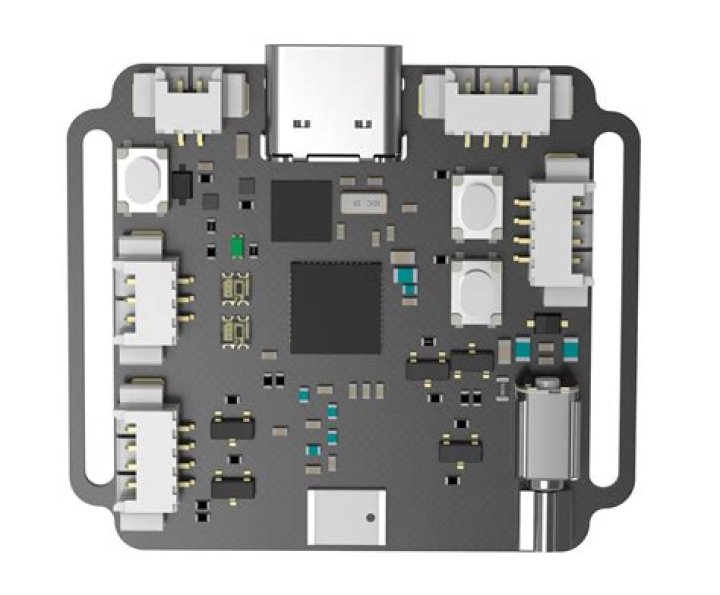
IoT VPC (Virtual Private Cloud) is a cloud-based infrastructure designed to securely host and manage IoT devices. By leveraging VPC, organizations can isolate their IoT networks from the public internet, reducing the risk of cyberattacks. Raspberry Pi, a compact and affordable single-board computer, serves as an ideal platform for connecting IoT devices to the cloud.
Using Raspberry Pi, you can create a bridge between your IoT devices and VPC, enabling seamless data exchange. This setup is particularly useful for applications such as home automation, industrial monitoring, and smart agriculture. However, ensuring secure communication is essential to protect sensitive data and maintain system integrity.
Throughout this article, we will delve into the technical aspects of setting up a secure IoT VPC connection using Raspberry Pi. By following the steps outlined, you can enhance the security of your IoT infrastructure and ensure reliable data transmission.
Setting Up Your Raspberry Pi for IoT VPC
Step 1: Hardware Requirements
Before diving into the software setup, ensure you have the necessary hardware components:
- Raspberry Pi (preferably Raspberry Pi 4 for better performance)
- MicroSD card with Raspberry Pi OS installed
- Power supply
- Network cable or Wi-Fi dongle
Step 2: Initial Configuration
Once your hardware is ready, follow these steps to configure your Raspberry Pi:
- Connect your Raspberry Pi to a monitor, keyboard, and mouse.
- Power on the Raspberry Pi and complete the initial setup process.
- Update the operating system using the following commands:
sudo apt update
sudo apt upgrade
These updates ensure that your Raspberry Pi is running the latest software versions, reducing the risk of vulnerabilities.
Understanding VPC Architecture for IoT
What is VPC?
A Virtual Private Cloud (VPC) is a virtual network dedicated to your AWS account. It allows you to launch AWS resources in a logically isolated section of the cloud. By configuring subnets, route tables, and security groups, you can control access to your IoT devices and ensure secure communication.
Key Components of VPC
- Subnets: Divides your VPC into smaller segments for better management.
- Route Tables: Defines how traffic is routed between subnets and external networks.
- Security Groups: Acts as a virtual firewall to control inbound and outbound traffic.
Understanding these components is crucial for designing a secure IoT VPC architecture. Proper configuration ensures that only authorized devices can access your network.
Security Protocols for IoT Connections
When connecting IoT devices to a VPC, it's essential to implement robust security protocols to protect against unauthorized access. Some of the most widely used protocols include:
- SSL/TLS: Encrypts data transmitted between devices and the cloud.
- SSH: Provides secure remote access to your Raspberry Pi.
- MQTT: A lightweight protocol designed for IoT communication, offering secure and efficient data transfer.
By leveraging these protocols, you can ensure that your IoT connections remain secure and resilient against cyber threats.
Implementing Encryption Methods
Why Encryption Matters
Encryption plays a vital role in securing IoT communications. It transforms plain text data into ciphertext, making it unreadable to unauthorized parties. This process ensures that even if data is intercepted, it cannot be deciphered without the proper decryption key.
Common Encryption Algorithms
- AES (Advanced Encryption Standard): Widely used for securing sensitive data.
- RSA: A public-key encryption algorithm commonly used for secure data transmission.
Implementing encryption on your Raspberry Pi involves configuring the necessary libraries and ensuring that all communication channels are encrypted.
Enabling Secure Remote Access
Remote access to your Raspberry Pi is essential for managing IoT devices and monitoring data. However, it's crucial to ensure that this access is secure to prevent unauthorized entry. Follow these best practices:
- Use SSH (Secure Shell) for remote access.
- Disable password authentication and use SSH keys instead.
- Restrict access to specific IP addresses using firewall rules.
By following these guidelines, you can securely connect to your Raspberry Pi from anywhere in the world.
Managing Data Download from IoT Devices
Automating Data Download
Downloading data from IoT devices can be automated using scripts and cron jobs. This approach ensures that data is regularly retrieved and stored for further analysis. Follow these steps:
- Create a script to fetch data from your IoT devices.
- Schedule the script using cron to run at regular intervals.
- Store the data in a secure location, such as an encrypted database.
Automation not only saves time but also reduces the risk of human error, ensuring that your data remains accurate and up-to-date.
Best Practices for Secure IoT Connections
To further enhance the security of your IoT VPC connection, consider the following best practices:
- Regularly update your Raspberry Pi and all connected devices.
- Implement multi-factor authentication for added security.
- Monitor network activity for suspicious behavior using intrusion detection systems.
By adhering to these practices, you can minimize the risk of security breaches and ensure the longevity of your IoT infrastructure.
Troubleshooting Common Issues
Even with the best security measures in place, issues may arise. Here are some common problems and their solutions:
- Connection Issues: Verify network settings and ensure that all devices are properly configured.
- Data Loss: Check storage configurations and implement regular backups.
- Security Breaches: Review security logs and update security protocols as needed.
Proactive troubleshooting can help you address issues before they escalate, ensuring uninterrupted operation of your IoT network.
Conclusion and Next Steps
In conclusion, securely connecting remote IoT VPC with Raspberry Pi is a critical step in building a robust and reliable IoT infrastructure. By following the steps outlined in this article, you can ensure that your IoT devices remain secure and that data transmission is seamless and efficient.
We encourage you to take the next steps by implementing the techniques discussed and exploring additional resources to further enhance your knowledge. Don't forget to share your thoughts and experiences in the comments below, and consider subscribing to our newsletter for more insightful content.