Free IoT SSH Login: Your Ultimate Guide to Secure Remote Access
As the Internet of Things (IoT) continues to expand, the demand for secure and free IoT SSH login solutions has skyrocketed. Organizations and individuals alike are searching for ways to access their IoT devices remotely without compromising security. In this comprehensive guide, we will explore everything you need to know about IoT SSH login, including its benefits, implementation, and best practices for maintaining security.
With billions of IoT devices now connected globally, the ability to manage and monitor them remotely has become essential. However, ensuring secure access remains a top priority. This is where SSH (Secure Shell) comes into play, offering a reliable method for encrypted communication between devices. Understanding how to implement free IoT SSH login can significantly enhance your operational efficiency.
This article aims to provide a detailed overview of IoT SSH login, covering everything from its basic principles to advanced configurations. Whether you're a beginner or an experienced user, you'll find valuable insights to help you secure your IoT infrastructure effectively.
Introduction to IoT SSH Login
The concept of IoT SSH login revolves around using the Secure Shell protocol to establish secure connections with IoT devices. SSH is a network protocol that provides encrypted communication between two systems, ensuring data integrity and confidentiality. By implementing SSH for IoT devices, users can remotely access and manage their devices without worrying about unauthorized access.
SSH is widely regarded as one of the most secure methods for remote access due to its robust encryption algorithms and authentication mechanisms. It is particularly beneficial for IoT devices, which often operate in unsecured environments and require additional layers of protection.
Why SSH is Essential for IoT
- SSH encrypts all data transmitted between devices, preventing eavesdropping.
- It supports strong authentication methods, such as public key authentication.
- SSH can be configured to run on various platforms, making it versatile for IoT use cases.
Why Use SSH for IoT?
When it comes to securing IoT devices, SSH offers several advantages over other protocols. Unlike unencrypted protocols such as Telnet, SSH ensures that all communication between devices is encrypted, reducing the risk of data breaches. Additionally, SSH supports advanced authentication methods, such as public key infrastructure (PKI), which enhances security by eliminating the need for passwords.
Another key benefit of using SSH for IoT is its compatibility with a wide range of devices and operating systems. From Raspberry Pi to industrial sensors, SSH can be implemented across various platforms, providing a standardized approach to remote access.
Security Features of SSH
- End-to-end encryption using algorithms like AES and RSA.
- Support for public key authentication, reducing the risk of brute-force attacks.
- Ability to configure firewall rules to restrict access to specific IP addresses.
Benefits of Free IoT SSH Login
Free IoT SSH login solutions offer numerous advantages for both individuals and organizations. By leveraging open-source SSH implementations, users can secure their IoT devices without incurring additional costs. These solutions often come with a wide range of features and community support, ensuring that users have access to the latest security patches and updates.
In addition to cost savings, free SSH implementations also provide flexibility in terms of customization. Users can tailor their SSH configurations to meet specific requirements, such as limiting access to certain users or enabling specific command-line tools.
Key Advantages of Free IoT SSH Login
- No licensing fees or subscription costs.
- Access to open-source communities for support and collaboration.
- Ability to customize configurations to suit specific use cases.
Setting Up SSH on IoT Devices
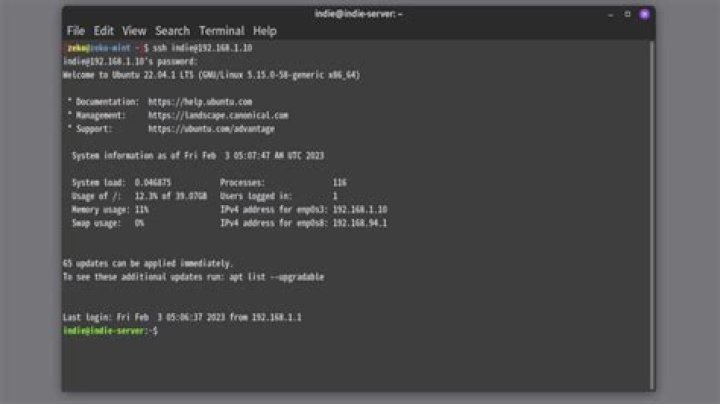
Setting up SSH on IoT devices involves several steps, including enabling the SSH service, configuring authentication methods, and securing the connection. Below is a step-by-step guide to help you get started:
Step 1: Enable SSH on Your IoT Device
Most IoT devices, such as Raspberry Pi or Arduino-based systems, come with SSH pre-installed but disabled by default. To enable SSH, follow these steps:
- Access the device's configuration menu or settings interface.
- Locate the SSH option and enable it.
- Save the changes and restart the device if necessary.
Step 2: Configure Authentication Methods
Once SSH is enabled, it's essential to configure authentication methods to ensure secure access. Public key authentication is recommended over password-based authentication due to its enhanced security. Here's how to set it up:
- Generate a public/private key pair on your local machine using tools like
ssh-keygen. - Copy the public key to the IoT device's authorized_keys file.
- Disable password authentication in the SSH configuration file (
/etc/ssh/sshd_config).
Securing Your IoT SSH Connection
Securing your IoT SSH connection is critical to protecting your devices from unauthorized access. Below are some best practices to enhance the security of your SSH setup:
Best Practices for SSH Security
- Use strong, unique passwords if password-based authentication is enabled.
- Limit SSH access to specific IP addresses using firewall rules.
- Regularly update SSH software to patch known vulnerabilities.
Additionally, consider implementing advanced security measures, such as two-factor authentication (2FA) or intrusion detection systems (IDS), to further protect your IoT devices.
Common SSH Commands for IoT
Once SSH is set up on your IoT device, you can use a variety of commands to manage and interact with it remotely. Below are some commonly used SSH commands for IoT:
Basic SSH Commands
ssh user@hostname: Connect to an IoT device via SSH.scp file user@hostname:/path: Copy files to or from the IoT device.ssh-keygen: Generate a public/private key pair for authentication.
These commands provide a foundation for managing your IoT devices remotely, enabling you to perform tasks such as file transfers, software updates, and configuration changes.
Troubleshooting IoT SSH Login
Despite its robustness, SSH connections can sometimes encounter issues. Below are some common problems and their solutions:
Common Issues and Solutions
- Connection Refused: Ensure that the SSH service is running on the IoT device and that firewall rules allow incoming SSH traffic.
- Authentication Failed: Verify that the correct username and authentication method (password or key) are being used.
- Timeout Errors: Check network connectivity and ensure that the IoT device's IP address is correct.
By addressing these issues systematically, you can resolve most SSH-related problems and maintain secure access to your IoT devices.
Best Practices for IoT SSH
To maximize the security and efficiency of your IoT SSH setup, consider adopting the following best practices:
Key Recommendations
- Regularly audit SSH configurations to ensure compliance with security standards.
- Implement role-based access control (RBAC) to limit user privileges.
- Monitor SSH logs for suspicious activity and take corrective action as needed.
By following these guidelines, you can ensure that your IoT devices remain secure and accessible only to authorized users.
Future Trends in IoT SSH Login
As the IoT landscape continues to evolve, so too will the methods used to secure remote access. Future trends in IoT SSH login are likely to include:
Emerging Technologies
- Quantum-resistant encryption algorithms to protect against future threats.
- AI-driven intrusion detection systems for real-time threat mitigation.
- Integration with blockchain technology for enhanced authentication and data integrity.
Staying informed about these advancements will help you prepare for the future of IoT security and ensure that your devices remain protected.
Conclusion and Next Steps
In conclusion, free IoT SSH login offers a secure and cost-effective solution for managing IoT devices remotely. By understanding the principles of SSH and implementing best practices, you can enhance the security of your IoT infrastructure and protect it from potential threats.
We encourage you to take the following steps:
- Review and update your SSH configurations to align with the best practices outlined in this article.
- Explore additional resources and communities to deepen your knowledge of IoT security.
- Share your thoughts and experiences in the comments section below or reach out to us for further assistance.
Thank you for reading, and we hope this guide has provided valuable insights into securing your IoT devices with SSH. For more information on IoT security and related topics, explore our other articles on the site.


