Best RemoteIoT SSH Key Management: A Comprehensive Guide to Secure Your Network
Managing SSH keys for remote IoT devices is essential in today's interconnected world. As more businesses adopt IoT technology, ensuring secure key management has become a top priority. Without proper SSH key management, sensitive data could be exposed to unauthorized access, leading to potential security breaches.
The importance of secure SSH key management cannot be overstated. With the rise of remote work and IoT devices, organizations need robust systems to protect their networks from cyber threats. This guide will explore the best practices for managing SSH keys in remote IoT environments, helping you safeguard your infrastructure.
By implementing effective SSH key management strategies, businesses can reduce vulnerabilities and enhance overall security. Whether you're a network administrator or an IT professional, understanding how to manage SSH keys in remote IoT systems is crucial for protecting valuable data and maintaining operational integrity.
Understanding SSH Keys in RemoteIoT
What Are SSH Keys?
SSH keys serve as digital certificates that authenticate users and devices in secure communications. In remote IoT environments, these keys enable encrypted connections between devices, ensuring data integrity and confidentiality. According to a report by Gartner, over 20 billion connected devices are expected by 2023, emphasizing the need for secure key management.
Key points about SSH keys:
- Provide secure authentication without passwords
- Enable encrypted communication between devices
- Reduce the risk of unauthorized access
Why Is SSH Key Management Important for RemoteIoT?
Effective SSH key management plays a vital role in securing remote IoT networks. Without proper management, organizations face significant risks, including unauthorized access, data breaches, and compliance violations. A study by IBM found that the average cost of a data breach in 2022 was $4.35 million, highlighting the financial impact of inadequate security measures.
Best Practices for RemoteIoT SSH Key Management
1. Use Strong Key Pairs
Generating strong SSH key pairs is the foundation of secure key management. Experts recommend using 2048-bit or higher RSA keys or ECC keys for enhanced security. Additionally, ensure that private keys are stored securely and never shared between devices.
2. Automate Key Rotation
Regular key rotation is essential for maintaining security in remote IoT environments. Automation tools can streamline this process, reducing the risk of human error. According to a survey by CyberArk, 70% of organizations believe automated key management improves security and efficiency.
3. Implement Access Controls
Establishing strict access controls ensures that only authorized users and devices can access sensitive information. Role-based access control (RBAC) systems can help manage permissions effectively, minimizing the risk of unauthorized access.
Challenges in RemoteIoT SSH Key Management
Managing SSH keys in remote IoT environments presents several challenges, including scalability, key expiration, and device proliferation. As the number of connected devices grows, organizations must adapt their key management strategies to accommodate these changes. A report by IDC predicts that IoT device growth will continue at a compound annual growth rate (CAGR) of 13.6% through 2025.
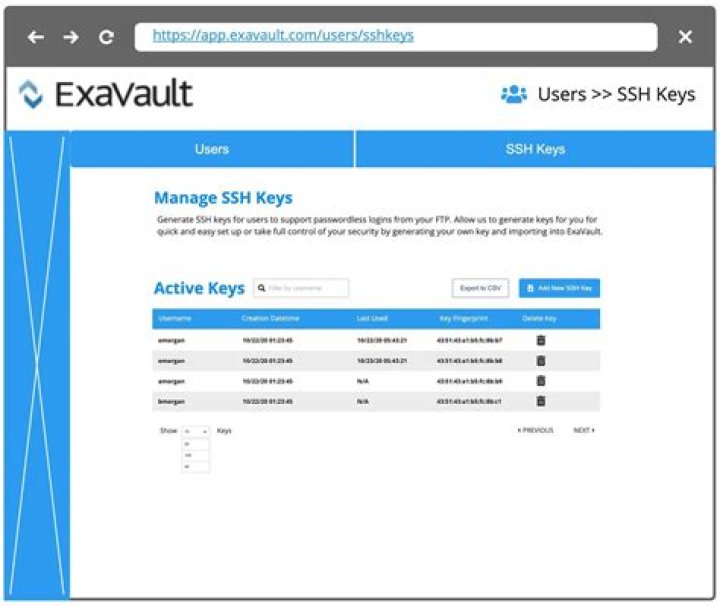
Tools and Solutions for SSH Key Management
1. OpenSSH
OpenSSH remains one of the most popular tools for managing SSH keys in remote IoT environments. Its open-source nature and extensive community support make it an attractive option for organizations seeking cost-effective solutions.
2. HashiCorp Vault
HashiCorp Vault offers advanced encryption and key management capabilities, making it ideal for securing sensitive data in remote IoT networks. Its dynamic secrets generation feature enhances security by eliminating the need for static keys.
3. CyberArk
CyberArk provides enterprise-grade solutions for managing SSH keys across complex IoT infrastructures. Its centralized management platform simplifies key rotation, access control, and compliance monitoring.
Security Considerations for RemoteIoT SSH Key Management
When implementing SSH key management in remote IoT environments, consider the following security best practices:
- Regularly audit key usage and access permissions
- Encrypt all sensitive data transmissions
- Monitor for suspicious activity and anomalies
- Comply with industry regulations and standards
Compliance and Regulatory Requirements
Organizations must adhere to various compliance standards when managing SSH keys in remote IoT environments. Regulations such as GDPR, HIPAA, and PCI-DSS require strict data protection measures, including secure key management practices. Failure to comply with these standards can result in significant fines and reputational damage.
Future Trends in RemoteIoT SSH Key Management
Advancements in technology continue to shape the future of SSH key management in remote IoT environments. Emerging trends include:
- Quantum-resistant cryptography
- Artificial intelligence-driven automation
- Zero-trust architecture implementation
Implementing a Comprehensive SSH Key Management Strategy
To ensure effective SSH key management in remote IoT environments, organizations should adopt a multi-layered approach. This includes:
- Developing clear policies and procedures
- Training employees on security best practices
- Investing in advanced tools and technologies
Conclusion
In conclusion, managing SSH keys in remote IoT environments is critical for maintaining security and protecting sensitive data. By following best practices, leveraging advanced tools, and staying informed about emerging trends, organizations can enhance their SSH key management strategies. We encourage readers to share their thoughts and experiences in the comments section below. Additionally, explore our other articles for more insights into remote IoT security and management.