Access IoT SSH Free Login: The Ultimate Guide to Secure Remote Connections
Accessing IoT SSH free login has become a vital aspect of modern technology. As the Internet of Things (IoT) continues to grow, secure remote access plays a critical role in managing devices and networks. In this guide, we will explore everything you need to know about IoT SSH free login, its benefits, and how it can be implemented effectively.
The rise of IoT devices has transformed the way we interact with technology. From smart homes to industrial automation, IoT has revolutionized various sectors. However, with this advancement comes the need for secure communication. SSH (Secure Shell) provides a robust solution for accessing IoT devices remotely without compromising security.
In this article, we will delve into the world of IoT SSH free login, discussing its importance, setup, and best practices. Whether you're a beginner or an experienced user, this guide will provide valuable insights into managing IoT devices securely.
Introduction to SSH
SSH, or Secure Shell, is a cryptographic network protocol that facilitates secure communication between devices over an unsecured network. It is widely used for remote login and other secure network services. When it comes to IoT devices, SSH provides a secure way to manage and interact with them remotely.
SSH operates on port 22 by default and uses encryption to protect data transmitted between devices. This ensures that sensitive information, such as login credentials and configuration data, remains secure during transmission.
How SSH Works
SSH establishes a secure connection through a series of cryptographic algorithms. Here's a brief overview of the process:
- Client initiates a connection to the server.
- Server authenticates the client using public key cryptography.
- Once authenticated, a secure session is established for communication.
Benefits of IoT SSH
Implementing SSH for IoT devices offers several advantages. Below are some of the key benefits:
- Enhanced Security: SSH encrypts all data transmitted between devices, reducing the risk of data breaches.
- Remote Access: With SSH, you can manage IoT devices from anywhere in the world, as long as you have an internet connection.
- Scalability: SSH can handle multiple devices simultaneously, making it ideal for large-scale IoT deployments.
- Automation: SSH enables automated tasks, such as firmware updates and data collection, improving efficiency.
Setting Up SSH for IoT Devices
Setting up SSH for IoT devices involves a few straightforward steps. Below is a comprehensive guide to help you get started:
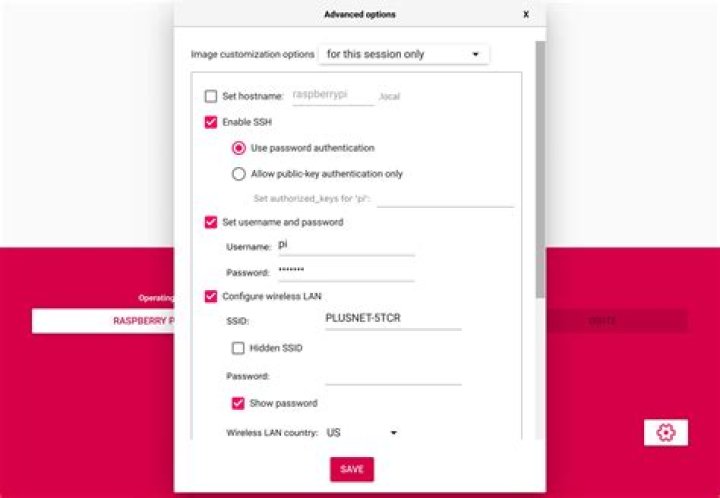
Step 1: Enable SSH on Your IoT Device
Most IoT devices come with SSH enabled by default. However, if it's not, you can enable it through the device's settings or configuration interface.
Step 2: Generate SSH Keys
To enhance security, it's recommended to use SSH keys instead of passwords for authentication. Here's how to generate SSH keys:
- Open a terminal or command prompt.
- Type
ssh-keygenand press Enter. - Follow the prompts to generate a public and private key pair.
Step 3: Configure SSH Server
Once SSH is enabled and keys are generated, configure the SSH server to accept connections. This involves setting up the correct port, enabling key-based authentication, and disabling password authentication.
Free SSH Options for IoT
There are several free SSH options available for IoT devices. Below are some of the most popular ones:
OpenSSH
OpenSSH is one of the most widely used SSH implementations. It is open-source and supports a wide range of platforms, making it ideal for IoT devices.
Dropbear
Dropbear is a lightweight SSH server and client, perfect for resource-constrained IoT devices. It offers similar functionality to OpenSSH but with a smaller footprint.
Security Considerations
While SSH provides a secure method for remote access, it's essential to follow best practices to ensure maximum security. Below are some key considerations:
- Use Strong Passwords: If you choose to use password authentication, ensure that your passwords are strong and unique.
- Enable Two-Factor Authentication: Add an extra layer of security by enabling two-factor authentication (2FA).
- Regularly Update Firmware: Keep your IoT devices and SSH software up to date to protect against vulnerabilities.
Best Practices for IoT SSH
Adopting best practices for IoT SSH can significantly enhance security and efficiency. Below are some recommendations:
Limit Access
Restrict SSH access to authorized users only. This can be achieved by configuring the SSH server to allow connections from specific IP addresses or networks.
Monitor Activity
Regularly monitor SSH activity to detect any unauthorized access attempts. This can be done by reviewing logs and setting up alerts for suspicious activity.
Troubleshooting Common Issues
Despite its robustness, SSH can sometimes encounter issues. Below are some common problems and their solutions:
- Connection Refused: Ensure that the SSH server is running and that the correct port is being used.
- Authentication Failed: Double-check your SSH keys and ensure that they are correctly configured on both the client and server.
- Timeout Errors: Check your network connection and ensure that there are no firewalls blocking the SSH port.
Alternatives to SSH
While SSH is the most popular method for secure remote access, there are alternatives worth considering:
Web-Based Interfaces
Some IoT devices offer web-based interfaces for management, which can be accessed through a browser. This eliminates the need for SSH but may not provide the same level of security.
VPN
Using a Virtual Private Network (VPN) can provide an additional layer of security for IoT devices. It encrypts all traffic between devices, ensuring data privacy.
The Future of IoT SSH
As IoT continues to evolve, so too will the methods used for secure remote access. Future developments in SSH for IoT may include:
- Quantum-Resistant Algorithms: To protect against future quantum computing threats, SSH may adopt quantum-resistant cryptographic algorithms.
- Improved Automation: Advances in artificial intelligence and machine learning could enhance the automation capabilities of SSH for IoT devices.
Conclusion
In conclusion, accessing IoT SSH free login is a crucial aspect of modern technology. By following the guidelines outlined in this article, you can ensure secure and efficient remote access to your IoT devices. Remember to adopt best practices and stay informed about the latest developments in IoT security.
We encourage you to share your thoughts and experiences in the comments section below. Additionally, feel free to explore other articles on our site for more insights into IoT and related technologies.
Data Source: SSH Protocol Overview, IoT For All


