Access IoT SSH AWS: A Comprehensive Guide to Secure Remote Access
Accessing IoT devices via SSH through AWS has become a critical skill for modern developers and IT professionals. The Internet of Things (IoT) continues to grow exponentially, with billions of devices now connected globally. Managing and maintaining these devices remotely is essential for ensuring security, efficiency, and scalability. By leveraging AWS services, organizations can establish secure and reliable SSH connections to IoT devices, enabling seamless remote access and management.
Remote access to IoT devices is not just about convenience; it is about ensuring operational continuity and enhancing productivity. AWS provides a robust infrastructure that supports secure communication channels, making it easier for businesses to manage their IoT ecosystems. This article explores the process of setting up SSH access for IoT devices using AWS, addressing security best practices, potential challenges, and practical solutions.
In this guide, we will delve into the technical aspects of configuring SSH access for IoT devices on AWS. From understanding the basics of IoT and SSH to implementing advanced security measures, this article aims to equip you with the knowledge and tools necessary to manage your IoT devices effectively. Let's dive in!
Introduction to IoT
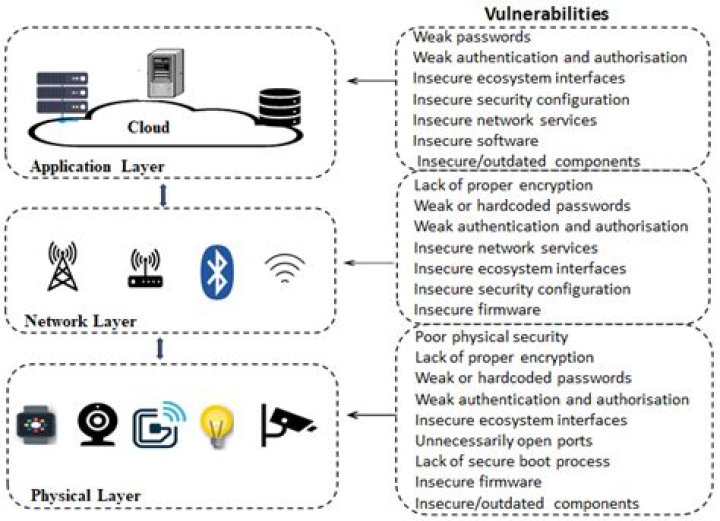
The Internet of Things (IoT) refers to the network of physical devices embedded with sensors, software, and connectivity, enabling them to exchange data with other devices and systems over the internet. IoT has revolutionized industries ranging from healthcare to manufacturing, providing unprecedented levels of automation and data-driven decision-making.
Key Components of IoT
- Devices: Sensors, actuators, and other hardware components.
- Connectivity: Wireless and wired communication protocols.
- Cloud Platforms: Services like AWS IoT Core that manage and analyze data.
- Data Analytics: Tools for processing and deriving insights from IoT data.
With the proliferation of IoT devices, managing them remotely has become a necessity. Secure remote access ensures that devices can be monitored, updated, and maintained without physical intervention, saving time and resources.
What is SSH?
SSH, or Secure Shell, is a cryptographic network protocol used for secure communication over unsecured networks. It provides a secure channel for remote command execution, file transfers, and other administrative tasks. SSH is widely used in IT environments to manage servers, network devices, and IoT systems.
Features of SSH
- Encryption: Protects data in transit from eavesdropping.
- Authentication: Ensures only authorized users can access the system.
- Integrity: Verifies that data has not been tampered with during transmission.
For IoT devices, SSH offers a secure way to access and manage them remotely, especially when combined with cloud platforms like AWS.
AWS IoT Core Overview
AWS IoT Core is a managed cloud service that allows connected devices to interact securely with cloud applications and other devices. It supports billions of devices and trillions of messages, making it scalable for large IoT deployments. AWS IoT Core provides features such as device management, messaging, and integration with other AWS services.
Key Features of AWS IoT Core
- Device Shadow: Maintains a virtual representation of a device's state.
- MQTT and HTTP Protocols: Supports multiple communication protocols.
- Rule Engine: Processes and routes IoT data to other AWS services.
By integrating SSH with AWS IoT Core, organizations can enhance the security and reliability of their IoT ecosystems, ensuring that devices can be accessed and managed remotely without compromising data integrity.
Setting Up SSH for AWS IoT
Configuring SSH access for IoT devices on AWS involves several steps, including setting up the necessary infrastructure, securing the connection, and testing the configuration. Below is a detailed guide to help you get started.
Step 1: Create an EC2 Instance
Begin by creating an Amazon EC2 instance that will act as the SSH server. Choose an appropriate instance type and configure the security group to allow SSH traffic on port 22.
Step 2: Connect IoT Devices to AWS IoT Core
Register your IoT devices with AWS IoT Core and configure them to communicate using MQTT or HTTP protocols. Ensure that each device has the necessary permissions and certificates for secure communication.
Step 3: Configure SSH Access
Set up SSH access by generating key pairs and configuring the SSH server on the EC2 instance. Use strong passwords and implement multi-factor authentication (MFA) for added security.
Security Best Practices
Security is paramount when accessing IoT devices via SSH on AWS. Below are some best practices to ensure your setup is secure:
1. Use Strong Authentication
Implement strong authentication mechanisms such as public key authentication and MFA to prevent unauthorized access.
2. Limit Access
Restrict SSH access to trusted IP addresses and use security groups to control inbound and outbound traffic.
3. Regularly Update Systems
Keep your EC2 instances and IoT devices up to date with the latest security patches and firmware updates.
Troubleshooting Common Issues
Despite careful planning, issues may arise when setting up SSH access for IoT devices on AWS. Below are some common problems and their solutions:
Issue 1: Connection Timeout
Solution: Verify that the security group allows SSH traffic and that the EC2 instance is running properly.
Issue 2: Authentication Failure
Solution: Double-check the SSH key pair and ensure that the correct username is being used.
Advanced Features
AWS offers several advanced features to enhance SSH access for IoT devices:
1. AWS Systems Manager
AWS Systems Manager provides a secure way to manage EC2 instances and IoT devices without exposing SSH ports to the public internet.
2. AWS IoT Device Defender
AWS IoT Device Defender monitors the behavior of IoT devices and detects anomalies that may indicate security threats.
Use Cases
Accessing IoT devices via SSH on AWS has numerous practical applications across various industries:
1. Remote Device Maintenance
IT teams can remotely troubleshoot and update IoT devices, reducing downtime and improving efficiency.
2. Data Collection and Analysis
Organizations can collect and analyze data from IoT devices in real-time, enabling data-driven decision-making.
Tools and Resources
To facilitate the setup and management of SSH access for IoT devices on AWS, consider using the following tools and resources:
1. AWS Management Console
The AWS Management Console provides a user-friendly interface for managing AWS services and resources.
2. AWS CLI
The AWS Command Line Interface (CLI) allows you to automate tasks and manage AWS resources from the command line.
Conclusion
Accessing IoT devices via SSH on AWS is a powerful solution for managing and maintaining IoT ecosystems. By following the steps outlined in this guide and implementing security best practices, organizations can ensure secure and reliable remote access to their IoT devices.
We encourage you to experiment with the tools and resources mentioned in this article and share your experiences in the comments section. For more insights and tutorials, explore our other articles on IoT, AWS, and cybersecurity.